
How Token Authentication Prevents Phishing
Token authentication is a game-changer in stopping phishing attacks by replacing passwords with secure digital tokens. Unlike traditional methods, tokens rely on cryptographic keys that are tied to specific devices and domains, making it nearly impossible for attackers to exploit stolen credentials. Here’s why it works:
- No Shared Secrets: Tokens eliminate the need for passwords, which are vulnerable to phishing and reuse.
- Device-Specific Security: Private keys stay on your device and can’t be extracted, even if attackers intercept data.
- Short Lifespan: Tokens expire quickly, limiting the time attackers can misuse them.
- Phishing Resistance: Cryptographic origin binding ensures tokens only work on legitimate websites.
For industries like healthcare and finance, where data protection is critical, token authentication reduces breaches and supports compliance with regulations like GDPR. By removing reliance on user judgment, this method builds stronger defenses against phishing.
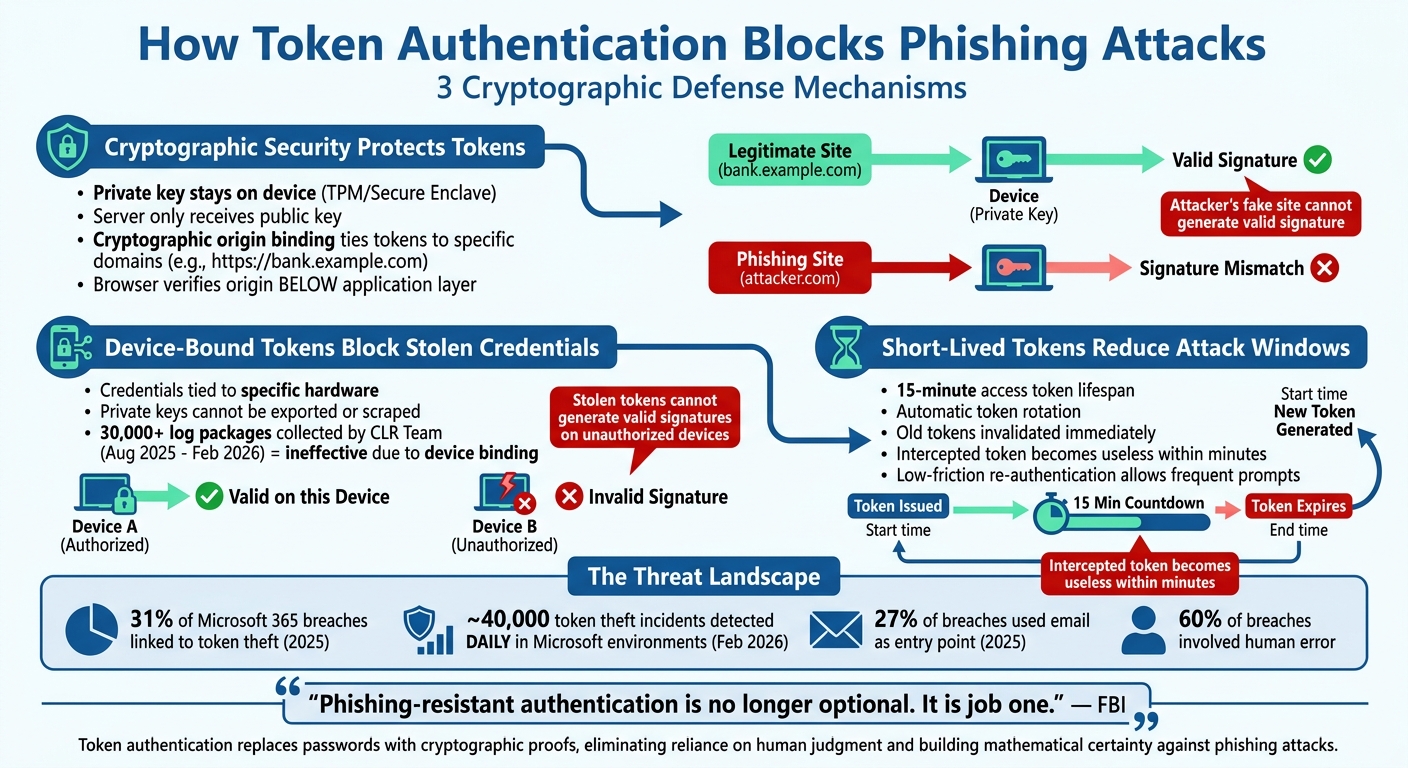
How Token Authentication Blocks Phishing Attacks: 3 Key Mechanisms
Token Theft Deep Dive Part 2: Prevention Techniques
sbb-itb-804866a
How Token Authentication Prevents Phishing
Token authentication eliminates phishing vulnerabilities by leveraging three key cryptographic mechanisms. These methods work seamlessly behind the scenes, removing the need for users to make judgment calls about whether a site is legitimate or not. Unlike passwords, which rely on human decision-making, tokens use cryptographic proofs that function below the application layer, offering a much stronger defense against phishing.
Cryptographic Security Protects Tokens
Token authentication replaces shared secrets with asymmetric cryptography. Here’s how it works: when you log in using a token-based system like WebAuthn, your device holds a private key securely stored in hardware-protected environments such as a Trusted Platform Module (TPM) or Secure Enclave. The server only receives the corresponding public key. Even if attackers replicate a login page perfectly, they gain nothing because the private key never leaves the device.
Another layer of security comes from cryptographic origin binding. When credentials are issued for a specific domain (e.g., https://bank.example.com), the browser records this origin and includes it in the authentication data. This data is then hashed and signed by the authenticator. Since this process occurs at the browser level - below where phishing attacks operate - a fraudulent site cannot generate a valid signature.
If an attacker attempts to use an Adversary-in-the-Middle (AiTM) proxy to relay your authentication request, the system detects the mismatch. The origin captured in the signature will reflect the attacker's domain rather than the legitimate one, causing the server to reject the request immediately.
"Passkeys... eliminate this entire class of vulnerability by replacing shared secrets with asymmetric cryptography and enforcing a property known as cryptographic origin binding".
Device-Bound Tokens Block Stolen Credentials
Device-bound tokens tie credentials to a specific piece of hardware, ensuring they cannot be exported or reused on unauthorized devices. Private keys stored in TPMs or Secure Enclaves are immune to being "scraped" from phishing forms or stolen in database breaches.
This makes captured credentials effectively useless. For example, an infostealer affiliate program called CLR Team reportedly collected over 30,000 log packages between August 2025 and February 2026, but the tokens remained ineffective since private keys never left the devices. Even as cybercriminals shift toward stealing session tokens - a growing trend as phishing-resistant MFA reduces the value of passwords - cryptographic binding ensures these tokens cannot generate valid signatures on unauthorized devices or in different network contexts.
The browser also plays a critical role by verifying that the Relying Party ID matches the current origin. The authenticator hashes the domain to locate the correct credentials, and these verification steps occur outside the attacker's control, creating a robust defense against phishing.
Short-Lived Tokens Reduce Attack Windows
Short-lived tokens add another layer of protection by limiting the time attackers have to misuse intercepted credentials. Many systems use 15-minute access tokens combined with refresh token rotation. This means new tokens are generated regularly, while old ones are invalidated immediately. If an attacker intercepts a token via phishing or an AiTM attack, it becomes useless within minutes.
"Short-lived tokens aren't just some security theater; they actually save your butt when things go wrong".
WebAuthn further strengthens this system by allowing organizations to prompt for re-authentication more frequently without frustrating users. Its low-friction process means users don’t mind verifying their identity more often, reducing the need for long-lived tokens and drastically lowering the risk of phishing.
"WebAuthn significantly reduces user experience friction and hence allows for more frequent authentication prompts, offsetting the need for long-lived tokens and significantly curbing the risk of phishing".
This continuous verification process ensures that attackers remain locked out, even if they manage to intercept an individual authentication attempt. These cryptographic protections naturally extend to secure messaging systems, which will be explored in the next section.
Implementing Token Authentication in External Messaging
Incorporating token-based authentication into external messaging platforms involves three essential components: cryptographic sender verification, end-to-end encryption, and centralized access controls. Together, these elements create a security framework that verifies sender identity, protects message content, and tightly manages access.
Cryptographic Sender Verification
To ensure message authenticity, platforms like Eleidon use Ed25519 digital signatures for sender verification. When an agent registers, a keypair is generated on the client side, keeping the private key securely stored on the device. The public key is linked to the agent’s inbox only after ownership is confirmed through a challenge-response mechanism.
Before sending a message, key fields such as From, To, Subject, Timestamp, and Body-Hash are standardized using ISO 8601 UTC formatting and hashed with SHA-256. The sender’s private key then signs this hash, which is included in a custom header like X-Eleidon-Signature: v1:<agent_id>:<signature_id>:<signature_hex>.
Recipients validate these signatures using a public API that compares the signature with the sender’s registered public key, providing a confidence score. A score of 1.0 confirms a valid signature from a verified sender, while a score of 0.0 or a "fraudulent" result highlights potential issues. This method surpasses traditional domain-based checks by directly verifying the agent.
"DKIM verifies domains. SPF verifies servers. Nothing verifies the agent on either end." - Eleidon
End-to-End Encryption Protects Messages
While sender verification confirms identity, securing message content requires a different layer of protection. End-to-end encryption ensures that only the intended recipient can access message content, using a zero-knowledge architecture that prevents even the platform from decrypting the data. This safeguard proved invaluable during the April 19, 2026 Vercel incident, where attackers exploited a malicious OAuth 2.0 app to compromise a Google Workspace account.
By pairing encryption with short-lived, rotating tokens, platforms minimize the risk of exploitation, even if other defenses are compromised.
Centralized Team Management Controls Access
Centralized management tools give organizations full control over access to messaging systems. Administrators can create, rotate, and manage signing keys through a unified Admin Center. Policies like limiting active keys to a maximum of 10 enhance security. This approach was critical in avoiding incidents like the Sacramento County breach in June 2021, where phishing exposed 2,096 health records, remaining undetected for five months.
Eleidon simplifies team management by enabling instant user additions or removals, enforcing domain-specific requirements, and providing detailed dashboards to monitor verification activity. Tokens and credentials are stored securely using environment variables and secrets managers, avoiding hard-coded sensitive data. Additionally, device attestation restricts access to approved, tamper-proof devices, further reducing risks.
"Treat credentials like a toothbrush - rotate them every three months and don't share them with others." - Twilio
Benefits for Healthcare, Law, and Financial Services
Protecting Sensitive Client and Patient Data
Token authentication acts as a strong cryptographic shield against attacks. For example, in one case, a stolen clinician's laptop posed no risk to patient data because the 15-minute tokens it relied on had already expired. This quick expiration prevented a potential HIPAA violation. Additionally, device-binding technologies, such as Microsoft’s Primary Refresh Tokens (PRTs), ensure that even if a token is intercepted, it cannot be used on another device. This level of protection is crucial, especially considering that Microsoft environments detect nearly 40,000 token theft incidents daily as of February 2026. These advanced defenses not only safeguard sensitive data but also help organizations meet strict data protection requirements.
Meeting GDPR and Regulatory Requirements
Token authentication doesn’t just stop threats - it also helps businesses stay compliant with regulations. For instance, it aligns with GDPR Article 32 by implementing rigorous technical and organizational controls. By utilizing scopes and claims, token systems ensure applications access only the specific data they need, minimizing exposure to personally identifiable information.
Organizations that adopt token-based authentication often experience fewer regulatory violations and reduced risk of fines. The European Union Agency for Cybersecurity (ENISA) highlights multi-factor authentication, which often incorporates tokens, as a recommended practice for securing systems that handle personal data.
"Token systems give you the audit trails and access controls you need. They help you avoid massive fines and legal trouble." - Jegan Selvaraj, Founder & CEO, Infisign
Building Client Confidence Through Security
In industries like healthcare, law, and finance, clients expect visible and reliable security measures. Token authentication delivers this by replacing traditional passwords with cryptographic methods. This ensures that even if someone clicks on a malicious link, authentication fails because the token is cryptographically tied to the legitimate domain.
This shift from relying on psychological defenses to mathematical certainty is critical in high-risk environments. For instance, email was the entry point for 27% of reported breaches in 2025, and human error, such as falling for social engineering, played a role in about 60% of all breaches.
Platforms like Eleidon take this even further by combining token authentication with cryptographic sender verification and end-to-end encryption. This creates a robust security framework that meets the demands of GDPR-compliant industries. Such measures reassure clients that their sensitive information is protected by proven technical safeguards. By eliminating vulnerabilities associated with passwords, token authentication also significantly reduces the effectiveness of phishing attacks, reinforcing trust and security in these critical sectors.
Conclusion
Token authentication is reshaping how organizations guard against phishing attacks by relying on cryptographic verification. This approach ties authentication to specific domains and devices, effectively removing the human errors that often undermine traditional security measures.
In 2025, 31% of Microsoft 365 breaches were linked to token theft, with nearly 40,000 token theft incidents detected daily in Microsoft environments. To counter these threats, using short-lived tokens, device binding, and phishing-resistant MFA - like FIDO2 security keys - adds layers of protection that are incredibly difficult for attackers to bypass. These methods also integrate smoothly with secure external messaging systems.
For industries handling sensitive data, this layered approach doesn’t just block breaches - it strengthens regulatory compliance and builds client trust. The FBI has made it clear: "Phishing-resistant authentication is no longer optional. It is no longer 'next phase.' It is job one." Moving away from password-based systems to cryptographic token authentication directly tackles the fact that compromised privileged credentials are a leading cause of data breaches.
Solutions like Eleidon showcase how token authentication can be combined with end-to-end encryption and centralized team management to create robust security frameworks. By incorporating features that support GDPR compliance, these platforms help organizations meet regulatory standards while reassuring clients about data protection.
This shift to token-based authentication moves the focus from hoping users avoid malicious links to ensuring that, even if mistakes happen, cryptographic safeguards block unauthorized access. For industries where a single breach can lead to regulatory fines, lawsuits, and damaged client relationships, this transition from relying on user behavior to mathematical certainty is the foundation of secure external messaging systems.
FAQs
How do tokens stop phishing even if I click a fake link?
Tokens are designed to combat phishing by being cryptographically linked to a specific device or session. This means that even if someone manages to steal a token, it can't be reused on a different device or exploited in replay attacks. Additionally, many systems employ proof-of-possession methods to confirm the token's legitimacy. This further limits unauthorized access, even in cases where a token has been compromised.
What’s the difference between device-bound tokens and session tokens?
Device-bound tokens are tied to a specific device through cryptographic techniques or device fingerprinting, ensuring they function exclusively on that device. This design helps protect against misuse, even if the token is stolen. On the other hand, session tokens are generated during login to keep a user authenticated throughout their session. Unlike device-bound tokens, session tokens aren't linked to a particular device, which makes them more vulnerable to interception unless extra security measures, such as cryptographic validation, are implemented.
How can Eleidon use token authentication to secure external messaging?
Eleidon strengthens external messaging security using token authentication to verify sender identities through cryptographic signatures. Here's how it works: every message is signed with a private key, and recipients validate its authenticity by comparing the signature with the sender's registered public key. This process ensures that messages are tamper-proof and come from trusted sources. By adding this phishing-resistant trust layer, Eleidon safeguards sensitive communications in sectors like healthcare, legal, and financial services.