
Secure Messaging for Financial Services: Complete Guide
Financial institutions face unique challenges in protecting sensitive data and meeting strict regulatory requirements. Unsecured messaging platforms like SMS and email expose firms to risks such as phishing, data breaches, and compliance violations. With over $3 billion in fines issued globally for "off-channel" communication failures, secure messaging is no longer optional - it’s essential for safeguarding sensitive information and avoiding penalties.
Key takeaways:
- Risks of unsecured messaging: Lack of encryption, phishing attacks, and human errors like misdirected emails.
- Regulatory requirements: Laws like GDPR, GLBA, and MiFID II mandate encryption, data retention, and secure communication channels.
- Secure messaging features: End-to-end encryption, multi-factor authentication, message revocation, and audit trails.
- Eleidon as a solution: Offers encrypted messaging, compliance features, and plans tailored for both individuals and financial firms.
Secure messaging platforms not only protect data but also ensure compliance with evolving regulations, such as the UK FCA's 2026 mandate for electronic communication as the default durable medium. By adopting tools like Eleidon, financial institutions can reduce risks and maintain trust in an increasingly regulated and threat-prone landscape.
Regulatory Requirements for Financial Messaging
Key Financial Regulations: GLBA, PCI DSS, GDPR, and SOX
Understanding the regulatory landscape is critical for financial institutions, especially when it comes to secure messaging. Regulations like the Gramm-Leach-Bliley Act (GLBA) require firms to encrypt customer data both in transit and at rest under the FTC Safeguards Rule. GLBA also mandates multi-factor authentication for system access and assigns a "Qualified Individual" to oversee security measures. Non-compliance can lead to hefty fines - $100,000 per violation for institutions and personal fines of $10,000, along with up to five years in prison for individuals.
For companies handling data from EU residents, GDPR is a key regulation. Article 32 of GDPR highlights encryption as a necessary measure for ensuring data security. Violators face penalties of up to €20 million or 4% of global turnover. GDPR also gives individuals the "Right to be Forgotten", a feature that secure messaging platforms address through tools like message revocation.
Investment services must also comply with MiFID II and FCA requirements, which require firms to retain all electronic communications related to transactions. These records must remain unaltered and accessible for at least five years. Similarly, SEC Rules 17a-3 and 17a-4, along with FINRA Rule 4511, require broker-dealers to store business communications securely and in a non-erasable format for a minimum of six years. Meanwhile, PCI DSS ensures the secure transmission of payment-related data across open networks.
Meeting Compliance Through Secure Messaging
Secure messaging platforms play a pivotal role in helping financial institutions meet these stringent regulatory demands. They offer automated archiving and recordkeeping, ensuring that SMS and instant messages are stored in formats compliant with SEC and FINRA standards. End-to-end encryption safeguards data both in transit and at rest, addressing multiple regulatory requirements.
Features like multi-factor authentication and conditional access policies protect sensitive financial data from unauthorized access, aligning with SOX and Dodd-Frank regulations. Advanced platforms also generate audit trails that document message access, timing, and actions like forwarding or revoking, providing critical evidence for compliance. Some even include information barriers, or "ethical walls", enabling administrators to control communication flows within the organization to prevent insider trading and conflicts of interest.
The push toward digital communication is intensifying compliance needs. Starting January 12, 2026, the UK's Financial Conduct Authority will require electronic communication to serve as the default durable medium for retail disclosures. Messaging systems must ensure that these communications are personally addressed, reproducible without alteration, and storable for future reference to meet FCA standards. Failure to comply has already resulted in fines exceeding $3 billion for poor handling of "off-channel" communications.
sbb-itb-804866a
Security Features Required for Financial Messaging
When it comes to financial messaging, standard security measures just don’t cut it. The sensitive nature of financial data demands stringent controls to safeguard against interception, unauthorized access, and even human error. These controls not only protect operational integrity but also ensure compliance with strict regulatory standards. Let’s dive into the key features that make secure financial messaging possible.
End-to-End Encryption and Sender Verification
End-to-end encryption (E2EE) ensures that messages are encrypted on the sender’s device and decrypted only on the recipient’s device. This means even if a message is intercepted or accessed on a server, it remains unreadable to unauthorized parties, including the service provider. Financial institutions should use AES-256 encryption as the baseline standard for securing data both at rest and in transit.
Sender and recipient verification adds another crucial layer of protection. By using trusted directories with verified participants, platforms can prevent unauthorized individuals from joining sensitive conversations. For highly sensitive communications, adding a second authentication step - like an SMS code or security question - ensures the recipient’s identity is thoroughly verified.
Another helpful safeguard is message revocation. This feature allows senders or administrators to retract messages, even after they’ve been read, minimizing the impact of misdirected communications and helping meet regulatory standards.
Multi-Factor Authentication
Multi-factor authentication (MFA) strengthens security by requiring multiple forms of verification: something the user knows (like a password), something they have (such as a hardware token or mobile device), and something they are (biometric data). Single-factor authentication simply doesn’t stand up to modern threats like phishing or automated password attacks.
For high-risk users, such as those with privileged accounts or remote access, MFA is a must. Advanced options like hardware-based cryptographic MFA, which stores authentication keys in secure modules, add even more protection. Out-of-band verification - where authentication happens through a separate channel - further defends against man-in-the-middle attacks.
Interestingly, Microsoft processes an astonishing 65 trillion signals daily to detect and counter identity-based threats. Many platforms are also moving toward passwordless authentication using FIDO2 standards, which rely on biometrics or security keys to reduce phishing risks. Combined with precise access controls, MFA becomes a cornerstone of secure financial messaging.
Access Controls and Zero-Trust Architecture
Access controls help define exactly who can view, share, or forward messages and files. Features like user entitlements, distinct room visibility for internal versus external participants, and information barriers prevent data leakage and reduce the risk of insider trading. Cryptographic isolation - using unique encryption keys for each conversation - ensures that a breach in one area doesn’t compromise the entire system. Financial firms can take this a step further with customer-managed keys, allowing them to retain full control over encryption via hardware security modules.
A zero-trust framework adds another layer of security by treating every access request as potentially risky. This approach requires comprehensive authentication, authorization, and encryption for every interaction. Conditional access policies that evaluate factors like device health, user location, and real-time risk scores add even more protection. With global email volumes running into the hundreds of billions daily, this level of vigilance is essential.
| Feature | Purpose | Threat Mitigated |
|---|---|---|
| E2EE (AES-256) | Data Confidentiality | Interception, Data Breaches |
| MFA | Identity Assurance | Unauthorized Access, Phishing |
| Revoke/Recall | Error Correction | Human Error, Misdelivery |
| Information Barriers | Internal Compliance | Insider Trading, Data Leakage |
| Audit Trails | Regulatory Evidence | Non-compliance, Fraud |
Audit trails are another critical feature. These logs meticulously record every action within the messaging system - who accessed what, when, and any actions like forwarding or revoking messages. This level of detail is invaluable for compliance audits and responding to incidents. For example, under UK GDPR, data breaches can lead to fines of up to £17.5 million or 4% of annual global turnover, whichever is higher. Such penalties highlight the importance of robust security and transparent record-keeping in financial messaging systems.
Using Eleidon for Secure Financial Messaging
Comparison of Eleidon Secure Messaging Plans for Financial Services
Eleidon steps in to address a critical gap for financial institutions: the choice between unsecured consumer apps and overly complex enterprise systems. It offers a secure, user-friendly messaging platform designed to meet the unique demands of the financial sector. With features like end-to-end encryption (E2EE) and multi-factor authentication, Eleidon ensures both data security and compliance with regulatory standards.
All messages sent through Eleidon are encrypted on the sender's device and decrypted only on the recipient's device, ensuring that even Eleidon itself cannot access the content. This approach significantly reduces risks, especially considering that human error accounts for 91% of data breaches.
The platform also employs Messaging Layer Security (MLS), a cutting-edge protocol for group communication that automatically updates encryption keys. Additionally, Eleidon integrates seamlessly with identity providers like Microsoft Entra ID, enabling Single Sign-On (SSO) and SCIM provisioning. This allows financial firms to maintain centralized control without disrupting existing workflows.
Eleidon’s trust request system adds another layer of security, requiring user approval for new contacts. This feature is particularly critical as cyberattacks on enterprises have surged by 58% between 2023 and 2025, with the average cost of a data breach projected to hit $4.4 million by 2025.
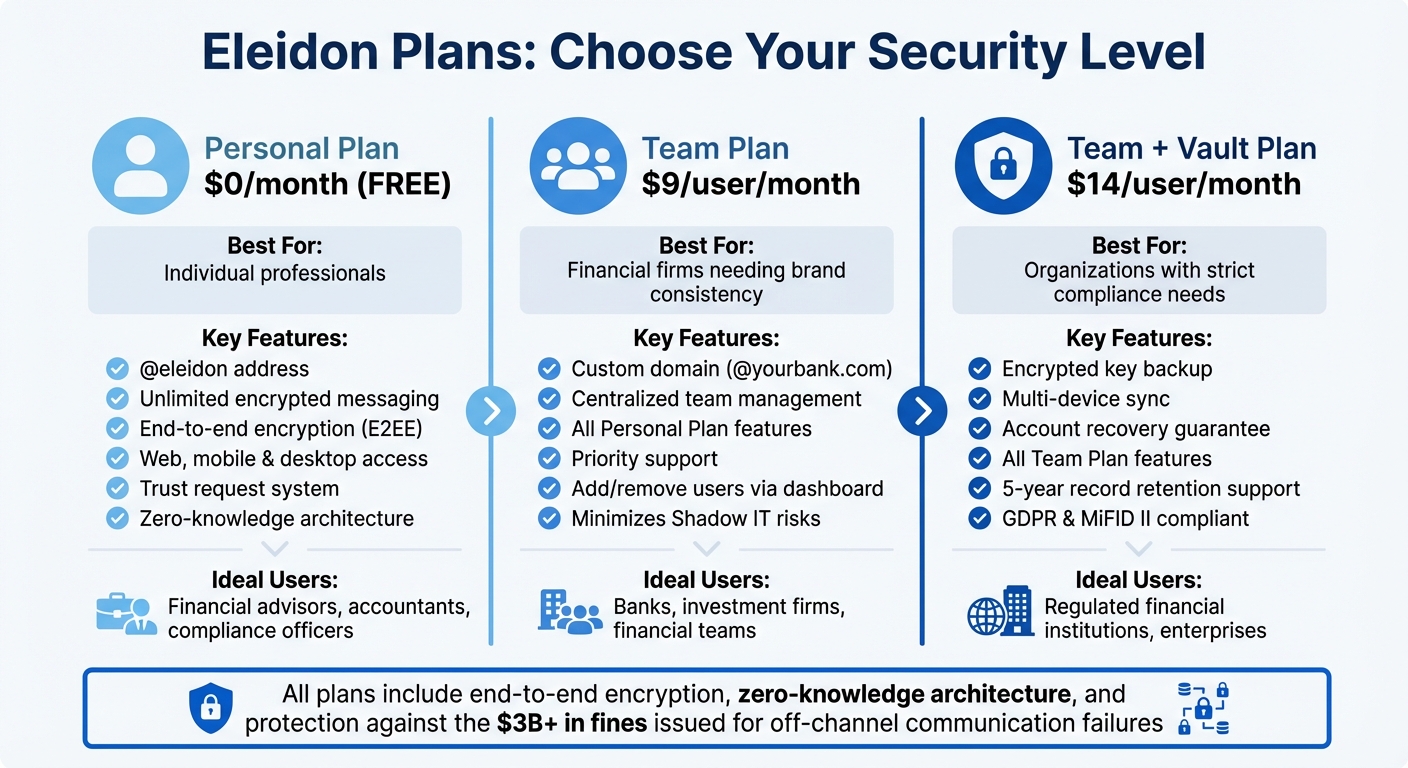
Eleidon Personal Plan Overview
The Personal Plan is a free option tailored for individual professionals who need secure communication. It provides users with an @eleidon address and supports unlimited encrypted messaging across web, mobile, and desktop platforms. Every message, file, and call is protected by E2EE, with encryption keys stored exclusively on the user’s device. This zero-knowledge approach ensures that even if Eleidon’s infrastructure were compromised, attackers would encounter only encrypted data.
This plan is particularly useful for financial advisors, accountants, or compliance officers who need to communicate securely with clients outside their organization. With no need for institutional approval or additional budgets, it’s a straightforward way to safeguard sensitive conversations. The trust request system further reduces phishing risks by giving users control over who can contact them.
For teams that require centralized management and advanced compliance features, Eleidon’s Team Plan offers a more comprehensive solution.
Eleidon Team Plan for Business Use
The Team Plan, priced at $9 per user per month, is designed for financial firms that need custom domain support and centralized team management. Organizations can replace generic @eleidon addresses with their own branded domains (e.g., @yourbank.com), maintaining a professional image while benefiting from secure E2EE. Administrators can easily add or remove team members via a central dashboard, ensuring immediate access changes when employees join or leave.
This plan helps address compliance challenges by minimizing Shadow IT risks and simplifying regulatory adherence. For instance, starting January 2026, the FCA recognizes electronic communication systems as the default durable medium for retail disclosures, provided they allow clients to store and reproduce records without alteration.
With priority support included, technical issues are resolved quickly, ensuring minimal disruption to critical financial operations. Centralized management also makes it easier for firms to enforce consistent security policies across all users.
Eleidon Team + Vault Plan for Enhanced Protection
The Team + Vault Plan, available at $14 per user per month, is designed for organizations requiring the highest level of security and compliance. Building on the Team Plan, it adds encrypted key backup, multi-device sync, and an account recovery guarantee - features that address the challenge of lost encryption keys in traditional E2EE systems.
The Vault feature securely stores encrypted backups of encryption keys, accessible only to the account owner. This ensures seamless data recovery without compromising the platform’s zero-knowledge architecture. For financial institutions required to retain records for five years under MiFID II, this feature is invaluable, keeping critical communications accessible for audits without exposing plaintext data.
The multi-device sync feature allows authorized users to securely access messages across desktop, mobile, and web platforms. Each device manages its own encryption keys, and the synchronization process is encrypted, ensuring security isn’t compromised. This is especially beneficial for financial professionals working across multiple locations in today’s hybrid work environments. Considering that GDPR violations can lead to fines of up to €20 million or 4% of global annual turnover, investing in a robust security solution like this is a wise choice.
| Plan | Monthly Cost | Best For | Key Differentiators |
|---|---|---|---|
| Personal | $0 | Individual professionals | @eleidon address, unlimited encrypted messages |
| Team | $9/user/month | Financial firms needing brand consistency | Custom domain, centralized management, priority support |
| Team + Vault | $14/user/month | Organizations with strict compliance | Encrypted backup, multi-device sync, account recovery guarantee |
How to Deploy Secure Messaging in Financial Services
Assessing Communication Security Risks
To ensure secure communication in financial services, the first step is understanding the risks involved. Financial organizations need to identify what they're protecting and pinpoint vulnerabilities in their communication systems. Start by analyzing the flow of Personal Identifiable Information (PII) through your channels. This includes direct identifiers like names and account numbers, indirect identifiers such as job titles and birth dates, and sensitive data like health or biometric information.
Everyday human error is a major risk - one in four people admit to sending personal data to the wrong recipient. This highlights the importance of evaluating your channels for encryption weaknesses, phishing risks, and the potential for misdelivery.
Regulatory compliance is another critical factor. Review obligations under GDPR for data protection, FCA COBS/SYSC for recordkeeping, and MiFID II for authentication and audit requirements. For example, as of January 12, 2026, the FCA recognizes electronic communication as a default "durable medium" for MiFID retail disclosures, provided it allows clients to store and reproduce information without changes. Evaluate potential communication tools against the NCSC secure communication principles, focusing on areas like encryption, access controls, audit features, and metadata protection.
| Assessment Area | Key Question for Financial Organizations |
|---|---|
| Data in Transit | Is data secured against eavesdropping and tampering with end-to-end encryption? |
| User Access | Does the platform support Multi-Factor Authentication (MFA) and secure admin controls? |
| Auditability | Are security events logged, and is there a tamper-proof audit trail? |
| Metadata | Is metadata collection minimized and protected from misuse? |
| Interoperability | Can users securely communicate with external partners without compromising security? |
Once risks are mapped, the next step involves a strategic rollout of secure messaging along with comprehensive staff training.
Rolling Out Secure Messaging and Training Staff
After identifying vulnerabilities, it's time to implement secure messaging systems and train your team. Staff education should focus on regulations, the basics of security, and practical ways to minimize risks. For example, employees should understand the "Puzzle Model of Identity", which explains how combining seemingly harmless data points - like a job title and birth date - can create high-risk PII that requires encryption. Training should also teach staff to identify spoofing attempts, where attackers impersonate trusted users to spread malicious links or misinformation.
Clear encryption policies are essential. For instance, require encryption for any communication containing personal data. Disable autofill features in email systems to reduce the chance of sending messages to the wrong recipient. Implement a "joiners, movers, and leavers" policy to ensure accounts are immediately deactivated when employees leave. Designate a compliance officer to oversee these processes and recommend appropriate security tools.
Practical training should include features like multi-factor authentication to verify client identities and using recall functions to retrieve misdirected emails. The ICO notes that if a misdirected email is successfully recalled before being read, it may not need to be reported as a data breach.
"One of the biggest misconceptions about secure email is that it's difficult to set up. In reality, the right solution can fit smoothly into existing workflows." - Paul Holland, Founder of Beyond Encryption
Monitoring Systems and Responding to Threats
Even with secure messaging and training in place, continuous monitoring is vital. Financial firms have faced over $3 billion in fines for poor practices in "off-channel" messaging. To avoid such penalties, maintain detailed audit trails that document message content, timing, and access for regulatory compliance and incident response. Use real-time tracking to monitor when messages are opened, forwarded, or downloaded, and by whom.
Enhance security with automated alerts that notify users or administrators when sensitive content is detected or when encryption is required. Integrate your messaging platform with tools like Data Loss Prevention (DLP) systems and malware scanners to block threats automatically. Administrative consoles can help compliance teams oversee message recalls, monitor communications, and track user behavior across the platform.
In the event of a data breach, the first 72 hours are critical. If a message is sent to the wrong recipient, attempt to recall it immediately. If that fails, formally request the recipient delete the message and document the action for the ICO. Under UK GDPR, fines for non-compliance can reach up to £17.5 million or 4% of global turnover, whichever is higher. Regular compliance audits can help detect suspicious activity, insider threats, or potential market abuse before they escalate into serious issues.
Preparing for Future Threats to Financial Communications
AI for Threat Detection
Artificial intelligence is reshaping how financial institutions tackle messaging threats. By using AI-driven behavior analysis within secure email gateways, institutions can identify and block phishing, spoofing, and malware in real time. This technology alerts employees before they send sensitive data to unfamiliar contacts, going beyond traditional signature-based detection methods.
Machine learning adds another layer of protection. It can prompt users during message composition and distinguish between genuine user behavior and automated brute-force attacks. Behavioral analysis also flags unusual activity that might signal a compromised account or insider threat. On top of that, automated compliance scanning ensures sensitive information is detected and encrypted in line with an institution's risk policies.
Quantum-Resistant Encryption Methods
While AI addresses today's challenges, the rise of quantum computing introduces new risks that require forward-thinking encryption strategies. Quantum computers, with their ability to use Shor's algorithm, could break widely used encryption methods like RSA and ECC, which are foundational to financial communications. The threat is amplified by "harvest now, decrypt later" tactics, where attackers steal encrypted data now, intending to decrypt it once quantum technology matures. Experts predict a 1 in 7 chance of public-key cryptography being broken by 2026, increasing to a 50% chance by 2031.
To counter this, the U.S. National Institute of Standards and Technology (NIST) finalized the first three post-quantum cryptography (PQC) standards in 2024: ML-KEM (formerly CRYSTALS-Kyber), ML-DSA (formerly CRYSTALS-Dilithium), and SLH-DSA (formerly SPHINCS+). These standards rely on lattice-based structures that are secure against both quantum and classical computing threats. Financial institutions are urged to embrace cryptographic agility, which allows them to swiftly switch between encryption algorithms. This starts with conducting a detailed cryptographic inventory and transitioning to hybrid models that combine new PQC algorithms with established classical methods.
"The transition to crypto agility is vital in maintaining the trust upon which the financial services sector is built and ensuring the safety of business operations in today's complex, ever-evolving computing environment."
– Michael Silverman, Chief Strategy & Innovation Officer, FS-ISAC
Some major platforms are already adapting. In February 2024, Apple introduced the "PQ3" protocol for iMessage, which merges classical ECC with post-quantum Kyber encryption. Similarly, in September 2023, Signal implemented Post-Quantum Extended Diffie-Hellman (PQXDH) to safeguard new conversations from future quantum threats. The EU has also outlined a coordinated PQC roadmap, requiring Member States to launch national transition strategies by December 31, 2026. Critical financial systems are expected to complete their transition by December 31, 2030. Financial institutions within the FS-ISAC network, which represents $100 trillion in assets across 75 countries, are leading this shift. By adopting quantum-resistant protocols, the financial sector can protect its communications from both current and emerging cyber threats.
Conclusion
Secure messaging has become a critical necessity for financial institutions. With over $3 billion in fines issued for off-channel communication failures and phishing attacks impacting 94% of financial organizations in the past year, the risks of neglecting secure communication are undeniable. On top of that, the average cost of a security breach in the financial sector has climbed to $6.08 million - 22% higher than in other industries.
These numbers underscore the pressing need for dependable secure messaging solutions. Beyond regulatory compliance with frameworks like GDPR, PCI DSS, and GLBA, maintaining secure communication is key to preserving client trust. Eleidon addresses these challenges with features like end-to-end encryption, robust sender verification, and a zero-knowledge design. Its trust request system eliminates phishing risks, while message revocation helps prevent human errors. For teams, the Team + Vault plan, priced at $14 per user per month, ensures encrypted key backups and account recovery - essential for regulatory compliance and business continuity.
As threats like quantum computing and AI-driven attacks become more sophisticated, financial institutions need messaging tools designed for durability and adaptability. Secure messaging not only ensures compliance but also protects the trust that forms the foundation of financial services. With the FCA mandating electronic communication as the default durable medium starting January 12, 2026, and regulators globally tightening cybersecurity mandates, early adoption of secure solutions will help institutions avoid costly updates and maintain client confidence in an evolving threat environment. By implementing advanced security measures today, financial organizations can ensure both compliance and trust as they navigate an increasingly challenging landscape.
FAQs
What is considered 'off-channel' messaging by regulators?
Regulators describe 'off-channel' messaging as any business-related communication that takes place on platforms not sanctioned, monitored, or recorded by the firm. This includes using third-party apps like WhatsApp, social media platforms, or even unapproved personal devices and applications. Since these interactions occur outside the firm's compliance framework, they can create regulatory challenges if left unmanaged.
How can we archive encrypted messages for SEC/FINRA audits?
To ensure encrypted messages are properly archived for SEC and FINRA audits, it's critical to use an archiving solution that meets compliance requirements. Look for a tool that securely captures and stores all electronic communications in formats that cannot be tampered with. The solution should automatically handle encrypted messages, apply retention policies, and use encryption to protect stored data.
Choose tools specifically designed for the financial services industry to align with regulations like SEC Rule 17a-4 and FINRA rules. These solutions should also make it simple to retrieve archived messages for audits and eDiscovery purposes.
What’s the best way to roll out secure messaging without hurting productivity?
To introduce secure messaging without disrupting productivity, it's all about thoughtful planning and encouraging users to embrace the change. Start by making messaging part of a larger mobility strategy. Plan the installation and testing phases carefully to avoid unnecessary interruptions. Choose software that's intuitive and easy to use, so employees can adapt quickly. Offering proper training and tailoring the solution to meet user needs will help ensure a seamless rollout, keeping productivity intact while boosting security.