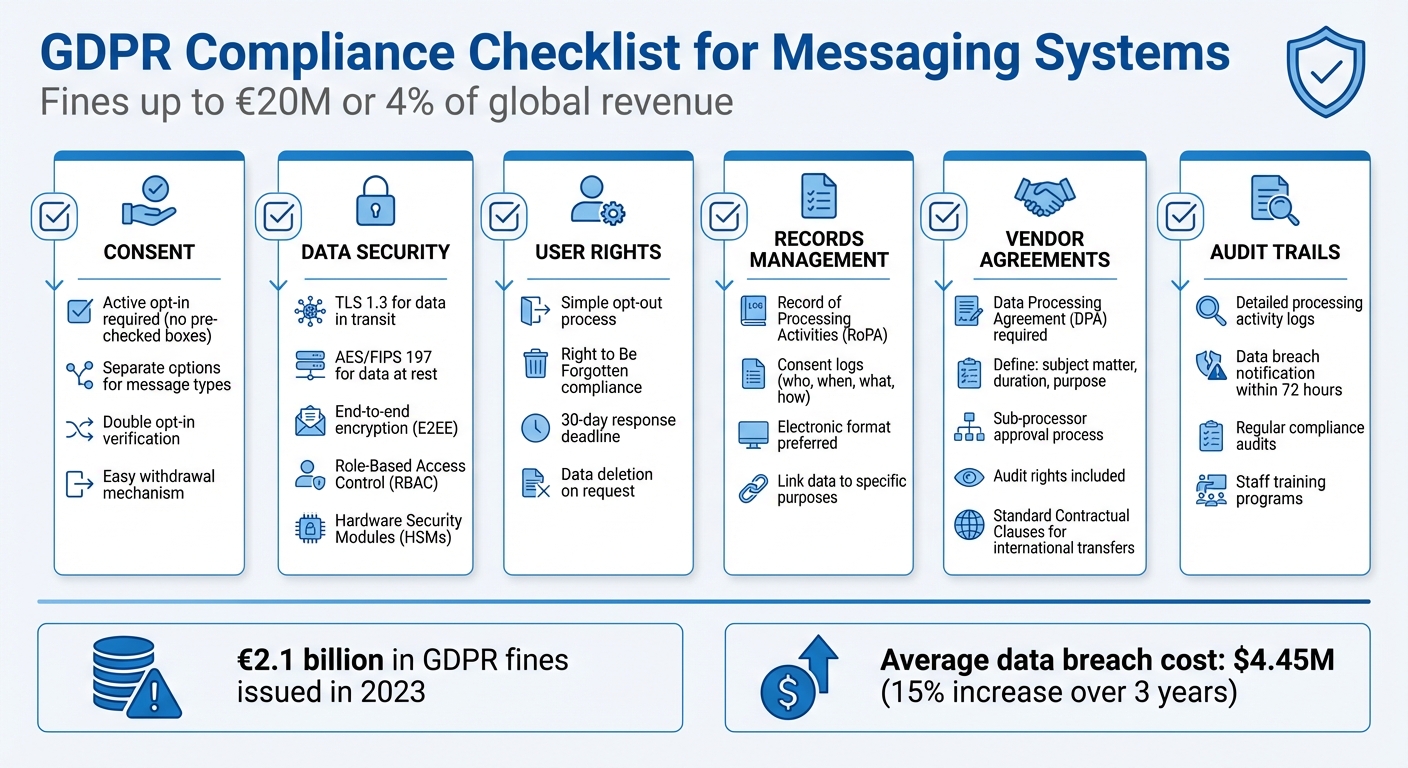
GDPR Compliance Checklist for Messaging Systems
GDPR compliance is essential for any messaging system handling EU citizen data. Noncompliance can result in fines up to $20 million or 4% of global revenue, so understanding the rules is critical. Here's what you need to know:
- Consent: Users must actively opt in, with clear options for different message types (e.g., transactional vs. marketing). Silence or pre-checked boxes don't count.
- Data Security: Use encryption (TLS 1.3 for data in transit, AES for data at rest) and implement Role-Based Access Control (RBAC) to limit access.
- User Rights: Make opting out and data deletion simple. Respond to 'Right to Be Forgotten' requests within 30 days.
- Vendor Agreements: Ensure third-party processors sign a Data Processing Agreement (DPA) covering security, data handling, and audit rights.
- Documentation: Maintain detailed records of data processing activities, consent logs, and breach reports.
GDPR Compliance Checklist for Messaging Systems: 6 Essential Requirements
User Consent and Legal Basis for Messaging
Setting Up Clear Consent Mechanisms
Under GDPR, valid consent requires users to take a clear, affirmative action. This means silence, inactivity, or pre-ticked boxes don't count as consent. Users need to actively opt in, such as by clicking a checkbox or tapping a specific button. When consent is collected as part of a written declaration covering multiple topics, the Information Commissioner's Office (ICO) highlights:
"If the data subject's consent is given in the context of a written declaration which also concerns other matters, the request for consent shall be presented in a manner which is clearly distinguishable from the other matters, in an intelligible and easily accessible form, using clear and plain language."
To ensure clarity, offer separate opt-in options for different types of messages - for instance, one for account notifications and another for promotional content. A double opt-in process - where users confirm their consent via email or SMS - adds another layer of verification and creates a reliable audit trail.
For sensitive data or automated decision-making, explicit consent is required. Make it easy for users to withdraw consent at any time and communicate this option clearly. A centralized preference dashboard can simplify this process, allowing users to manage their messaging settings effortlessly. Additionally, documenting every consent action is essential for maintaining compliance.
Recording and Storing Consent Logs
Once consent is obtained, it’s crucial to log it systematically. Article 7 of GDPR mandates that organizations must be able to demonstrate user consent to data processing. This means keeping detailed records for as long as the data is being processed. These logs should include:
- Who consented (e.g., user ID)
- When consent was given (timestamp)
- What information was presented (e.g., the version of the privacy notice)
- How consent was obtained (e.g., opt-in checkbox or button)
Each consent record should be linked to the specific privacy notice shown at the time of opt-in. If your messaging practices change, you’ll need to obtain new consent and update your records. To ensure data integrity, cryptographic hash functions can be used for online systems.
The ICO advises using electronic records instead of paper for easier access and sharing during audits. If a user withdraws consent, this action must also be documented. For marketing purposes, you may need to maintain a suppression list; in such cases, record the legal justification for retaining those records. Even smaller organizations (fewer than 250 employees) must document processing activities if they involve special category data or pose risks to individual rights.
sbb-itb-804866a
Data Security: Encryption and Access Controls
Encryption Standards for GDPR
Under GDPR Article 32, encryption is highlighted as an essential safeguard to maintain security proportional to potential risks. The Information Commissioner's Office (ICO) explains it clearly:
"Encryption is a process that uses a secret key to encode data, ensuring only those with access to the key can read it. It provides a suitable safeguard against any unauthorised or unlawful processing of personal information."
To meet these requirements, you need to implement two key types of encryption. First, protect data in transit using TLS 1.3 (steer clear of outdated SSL protocols). Second, secure data at rest with standards like FIPS 197 (AES). For maximum security, consider end-to-end encryption (E2EE), which ensures that only the sender and recipient can access the data, keeping it safe from everyone else.
Avoid creating custom encryption methods; instead, rely on trusted, certified solutions. The UK's National Cyber Security Centre (NCSC) offers a Certified Assisted Products Scheme (CAPS) that lists approved encryption tools.
Key management is just as important as encryption itself. The ICO cautions that storing encryption keys alongside the encrypted data renders the encryption meaningless. Use Hardware Security Modules (HSMs) for secure key storage and implement automated key rotation to limit exposure. As computing technology evolves, regularly reassess your encryption strategies to ensure they remain effective against modern threats.
Setting Up Role-Based Access Control
Encryption is only part of the equation - controlling access to decrypted data is equally critical. GDPR Article 32 emphasizes Role-Based Access Control (RBAC) as a key strategy for limiting access based on specific roles within your organization. For example, employees in Legal, IT, HR, or Sales should only access data relevant to their job responsibilities.
RBAC should include detailed permissions to regulate who can export, delete, or archive data. For instance, only compliance officers should handle "right to be forgotten" requests. Strengthen security further by requiring two-factor authentication (2FA) for anyone with access to personal data. Follow the principle of least privilege - no single individual should have full access to both encrypted data and its decryption keys.
Regular audits are essential to maintaining secure access control. Review role assignments periodically to ensure that employees who have changed roles or left the company no longer have access to sensitive information. With the global average cost of a data breach climbing to $4.45 million in 2023 - a 15% rise over three years - investing in strict access controls isn’t just a compliance measure; it’s a smart financial decision.
User Rights and Preferences Management
Processing Opt-Out Requests
Under GDPR, opting out must be just as straightforward as opting in. The Information Commissioner’s Office (ICO) highlights that individuals should be able to opt out at any time, not just by replying to a message.
Once an opt-out request is received, stop processing direct marketing data immediately. Automating this process ensures timely compliance. Always include clear unsubscribe links or phone numbers in your messages, and offer the same method for withdrawal that was used to opt in.
While you must cease processing immediately, it’s acceptable to maintain suppression records to ensure users aren’t contacted again by mistake. Be transparent about this practice in your privacy policy. Additionally, verify the identity of the requester before making changes, and ensure that withdrawing consent doesn’t lead to penalties or negative outcomes.
These steps lay the groundwork for handling 'Right to Be Forgotten' requests effectively.
Right to Be Forgotten Compliance
Handling deletion requests is a critical part of GDPR-compliant practices. However, the 'Right to Be Forgotten' has limitations. According to the ICO:
"The right to erasure is also known as 'the right to be forgotten'. The right is not absolute and only applies in certain circumstances."
Typically, you must respond to deletion requests within one month, though this can be extended to two months for more complex cases. Retain data only when legally required, and for backup systems, mark data as ‘beyond use’ until it’s overwritten according to your retention policy.
Your platform may decline deletion requests if retaining the data is necessary to comply with legal obligations or to establish, exercise, or defend legal claims. In such cases, document your reasoning and inform the individual of their right to file a complaint with a regulator.
The ICO provides this guidance:
"The key issue is to put the backup data 'beyond use', even if it cannot be immediately overwritten."
If personal data has been shared with third parties or published online, take reasonable steps to notify those parties about the erasure. Ensure your staff is trained to log and process erasure requests without delay.
Vendor Management and Data Processing Agreements
Required Elements in a GDPR-Compliant DPA
Before any messaging vendor can handle personal data, they must sign a Data Processing Agreement (DPA). This is a non-negotiable requirement under GDPR Article 28. The agreement must clearly define key processing details, such as:
- Subject matter: For instance, "user chat logs" or "contact lists."
- Duration: How long the data will be processed.
- Purpose: Examples include "providing instant messaging services."
- Types of personal data: This could include names, IP addresses, or message content.
- Data subjects: Identifying the individuals whose data will be processed.
The vendor is obligated to follow your instructions for processing data, maintain confidentiality among its personnel, and implement effective security measures. GDPR Recital 81 emphasizes:
"When entrusting a processor with processing activities, the controller should use only processors providing sufficient guarantees, in particular in terms of expert knowledge, reliability and resources, to implement technical and organisational measures which will meet the requirements of this Regulation, including for the security of processing."
Your DPA should also address sub-processor management. This means requiring prior written approval for any sub-processor changes and establishing a notification process so you can object if necessary.
Additionally, the agreement must grant audit rights, allowing you to inspect the vendor's systems and verify compliance. It should also specify that, once the contract ends, the vendor must either delete or return all personal data based on your instructions. Many vendors offer pre-prepared DPAs that meet Article 28's requirements, but it’s crucial to review them carefully.
Once the DPA is in place, the focus shifts to actively assessing your vendor's compliance.
Evaluating Vendor Compliance
Ensuring your vendor has the tools and expertise to protect data isn’t a one-and-done task - it’s an ongoing responsibility .
Start with an information audit to map out all third-party services that interact with your messaging data, from analytics platforms to cloud storage providers . Use questionnaires to gather details on data location, retention policies, and security measures. Review the vendor’s standard DPAs (often available on their websites) to confirm they address the necessary GDPR Article 28 requirements .
Pay special attention to technical security measures. Check if the vendor uses practices like end-to-end encryption, pseudonymization, or anonymization - methods strongly endorsed by GDPR when applicable . Confirm that they also have mechanisms to assist with Data Protection Impact Assessments and responses to data subject rights requests .
For vendors operating outside the UK or EU, ensure the DPA includes safeguards for international data transfers, such as Standard Contractual Clauses. Review their sub-processor list thoroughly and require advance notice of any changes. Lastly, the vendor must agree to audits and provide any necessary information to demonstrate compliance .
Audit Trails and Documentation Requirements
Documenting Data Processing Activities
Keeping a detailed record of your data processing activities is crucial for staying audit-ready. Under GDPR Article 30, both controllers and processors are required to maintain a Record of Processing Activities (ROPA). These records should ideally be in electronic format to make updates and audits more efficient.
As a controller, your ROPA must include several key details, such as:
- Name and contact information for your organization and Data Protection Officer (DPO)
- Purposes of processing (e.g., "providing instant messaging services")
- Categories of data subjects (e.g., "customers" or "employees")
- Categories of personal data (e.g., "IP addresses", "message content", or "contact details")
- Recipients of the data
- Information on international data transfers
- Retention or erasure timelines
- A description of your security measures
Processors have their own set of requirements, including documenting the name and contact details of your organization, the controllers you work with, your DPO, the categories of processing you handle, any international transfers, and your security measures.
The Information Commissioner's Office (ICO) stresses the importance of specificity and meaningful connections in your documentation:
"The record of your processing activities needs to reflect these differences. A generic list of pieces of information with no meaningful links between them will not meet the UK GDPR's documentation requirements."
For messaging systems, this means detailing activities like message delivery, user interactions, and consent changes, ensuring each data type is linked to its specific purpose. For example, connect "IP address" to "Customer Orders" and "Customers" rather than listing them separately. Organizations with fewer than 250 employees are generally exempt from Article 30, except when processing involves special category data, occurs regularly, or poses risks to individuals' rights and freedoms.
Organizing Records for Audits
Once your processing records are in place, proper organization is key to handling both internal and external audits. Regular updates to your documentation are essential, especially as your messaging platform evolves.
A "broad to narrow" strategy works well: start by organizing records by business functions like Customer Service, HR, or Sales, then drill down into specific purposes and data categories. To gather the necessary details, use internal questionnaires written in plain language to collect input from IT teams (for security protocols), Information Governance teams (for retention schedules), and Legal teams (for data-sharing agreements).
Leverage electronic tools to simplify this process, enabling quick updates and easy access for supervisory authorities when needed. Many organizations begin with templates provided by the ICO, while larger companies often turn to specialized software to handle more complex records.
In addition to the ROPA, maintain other critical documentation, such as:
- Consent logs showing when and how consent was obtained
- Data Protection Impact Assessment (DPIA) reports
- Records of personal data breaches
If a data breach occurs, remember you must notify authorities within 72 hours. Ensure all these documents are interconnected to facilitate seamless audits.
The ICO underscores the value of thorough documentation:
"Documenting your processing activities is important, not only because it is itself a legal requirement, but also because it can support good data governance and help you demonstrate your compliance."
Lastly, safeguard your documentation with robust security measures to ensure its confidentiality, integrity, and availability. This not only protects sensitive information but also reinforces your compliance efforts.
GDPR Compliance Checklist - A 12 Step Guide for you
Conclusion: GDPR Compliance Checklist Summary
Ensuring GDPR compliance for messaging systems is not a one-time task - it’s an ongoing commitment. As Thoropass aptly puts it:
"Adhering to GDPR standards is an evolving process rather than a final goal. This process necessitates continuous alertness, perpetual learning, robust procedures, and a strong data privacy culture".
With financial penalties reaching nearly €2.1 billion in 2023, the stakes couldn’t be higher. To navigate this landscape, your compliance strategy should focus on six core pillars:
- Explicit user consent: Ensure opt-out mechanisms are available and easy to use.
- Data security: Implement end-to-end encryption and Role-Based Access Control (RBAC).
- User rights: Fulfill user requests, including data erasure, within the required 30-day timeframe.
- Records management: Maintain comprehensive Records of Processing Activities (RoPA).
- Vendor agreements: Formalize Data Processing Agreements (DPAs) with all third-party vendors.
- Audit trails: Keep detailed logs to track and monitor data access and processing.
These pillars aren’t just technical requirements - they need to be part of your everyday operations to maintain strong data protection practices.
Integrating privacy into daily workflows is critical. Use enterprise-grade messaging platforms, automate data retention policies, and conduct Data Protection Impact Assessments (DPIAs) for every new feature. By weaving these practices into your operations, you ensure both security and trustworthiness.
Additionally, rapid breach response is non-negotiable. Establish protocols to meet GDPR’s 72-hour breach notification rule.
"When privacy becomes part of your company's daily practice, compliance stops being a challenge and starts becoming a strength." – MailSPEC
Regular maintenance of your compliance framework is just as important. Schedule annual audits - or more frequent reviews if your systems undergo significant changes - and invest in ongoing staff training to reduce human error. Keep your messaging data within GDPR-compliant jurisdictions to avoid unnecessary risks. With the average cost of a data breach climbing to $4.45 million in 2023 - a 15% increase over three years - proactive compliance not only safeguards your business but also fosters trust with your users. Regular audits and training are critical to sustaining this cycle of vigilance and accountability.
FAQs
How can messaging systems ensure user consent complies with GDPR requirements?
To meet GDPR standards for user consent in messaging systems, always request clear and explicit opt-in consent. Use simple, straightforward language - skip the legal jargon - and present the consent request on its own, separate from any other terms or conditions. Make sure users can easily understand what they’re agreeing to and offer a hassle-free way for them to withdraw consent whenever they choose.
Keep thorough records of consent, including details like who gave it, the date and method of collection, and the exact information shared at the time. Regularly review your consent procedures to ensure they stay compliant and, if needed, refresh user consent periodically. The focus should always be on transparency and giving users control over their data.
What steps can messaging systems take to manage and document user data processing activities under GDPR?
To align with GDPR requirements, messaging systems must keep precise and thorough records detailing how user data is handled. These records should cover key aspects like the purpose of data collection, the types of data being processed, who can access it, any transfers to third parties, and the retention period for the data.
Frequent reviews and updates of these records are essential to ensure they match current practices and comply with Article 30 of GDPR. On top of that, having well-defined policies and workflows to monitor user consent and data usage can showcase accountability and promote transparency in managing user information.
What should a GDPR-compliant Data Processing Agreement for messaging vendors include?
When working with messaging vendors, a GDPR-compliant Data Processing Agreement (DPA) needs to spell out essential details. This includes the purpose of data processing, the types of personal data involved, and the categories of individuals whose data will be processed. Additionally, it should define the duration of processing and clarify the responsibilities of both parties.
A solid DPA also requires commitments to key practices, such as:
- Processing data strictly according to documented instructions.
- Implementing robust security measures to protect the data.
- Ensuring full alignment with GDPR requirements.
Both parties should also agree to support audits and assist with requests related to data subject rights when necessary. By using clear and specific terms, the agreement fosters accountability and helps maintain compliance with GDPR.