Contact Approval Systems vs Traditional Email Filters
Email remains a primary target for cyberattacks, with phishing attempts and Business Email Compromise (BEC) causing billions in damages annually. Two key methods to combat these threats are Contact Approval Systems and email filters. Here's the difference:
- Email Filters: Analyze content, sender reputation, and technical headers to block spam and malicious emails. They're effective against bulk threats but struggle with sophisticated attacks like BEC or zero-day exploits.
- Contact Approval Systems: Focus on verifying sender identity through cryptographic authentication, blocking impersonation and spoofing. They excel at stopping targeted attacks but require initial setup and manual management.
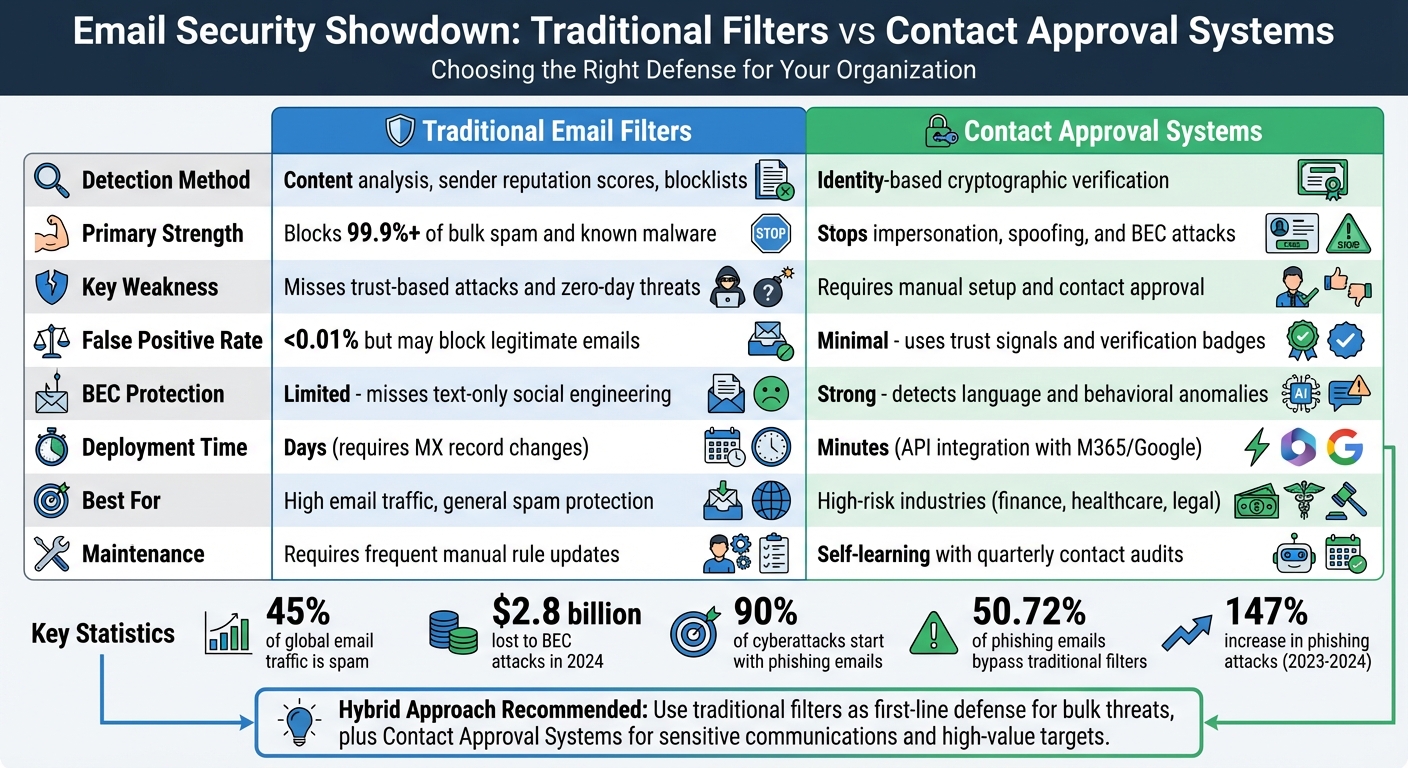
Quick Comparison
| Feature | Email Filters | Contact Approval Systems |
|---|---|---|
| Detection Method | Content analysis, reputation scores | Identity-based verification |
| Strengths | Blocks bulk spam, easy to deploy | Stops impersonation and targeted BEC |
| Weaknesses | Misses advanced, trust-based attacks | Requires manual setup and management |
| Best For | High email traffic, general use | High-risk, sensitive communications |
Both systems serve different needs. Filters work well for general spam protection, while Contact Approval Systems are better for industries like finance or healthcare, where email security is critical.
Traditional Email Filters vs Contact Approval Systems Comparison Chart
Episode 36 - Reduce phishing success with email controls that block, warn, and verify safely
sbb-itb-804866a
What Are Traditional Email Filters?
Traditional email filters work by examining incoming emails to determine whether they should land in your inbox or be blocked. They do this by analyzing IP reputations, email headers, and scanning content for suspicious elements like spammy patterns or malicious links. At the network level, these filters check DNS-based blacklists (DNSBLs) to assess the sender's IP history and verify protocols like SPF, DKIM, and DMARC to confirm the sender's legitimacy.
These systems rely on rule-based logic and statistical models. Essentially, they assign scores to potential red flags - things like excessive use of capital letters, spammy keywords such as "FREE" or "ACT NOW", or poorly formatted HTML. If the score exceeds a set threshold, the email is flagged as spam and either quarantined or sent to the spam folder. Bayesian filters are a key component of this process, using word frequency analysis to calculate the likelihood of an email being spam, often achieving about 98% accuracy.
"Email security systems operate like digital bouncers at the club entrance of your inbox. They analyze each message to decide delivery or quarantine."
_ - Javid, MailDiver_
These traditional methods form the backbone of how email filters operate.
Key Features of Traditional Email Filters
Traditional filters rely on a multi-layered approach to detect spam and malicious emails. They scan for suspicious keywords, unusual image-to-text ratios (a common spam tactic), and malicious links embedded in the email body. Header analysis is another critical tool, helping to identify inconsistencies in SMTP transactions, such as forged sender addresses or unusual routing paths that might signal spoofing attempts.
Some filters incorporate machine learning models, including neural networks, to catch more complex patterns that static rules might miss. For instance, emails with more than 40% of their content as images are often flagged, as this is a common trick spammers use to bypass keyword scans. Considering that spam makes up roughly 45% of all global email traffic, these detection mechanisms are crucial.
However, even with these advanced features, traditional filters face some notable challenges.
Common Problems with Email Filters
One of the biggest hurdles for traditional email filters is managing false positives (legitimate emails mistakenly flagged as spam) and false negatives (malicious emails that slip through). For example, critical emails like password reset requests or transactional messages can sometimes be misclassified, causing disruptions to everyday workflows. Attackers also use clever evasion techniques, such as replacing letters with similar-looking characters (e.g., "m0ney" instead of "money") or employing "Bayesian poisoning" - adding random, legitimate words to malicious emails to reduce their spam score.
Another significant challenge is dealing with zero-day threats and social engineering attacks. Since traditional filters rely on known patterns and historical data, they can miss new types of attacks, like those originating from freshly registered domains or compromised legitimate accounts. On top of that, attackers increasingly use AI to create highly convincing and personalized emails that mimic genuine internal communications, making them incredibly hard to detect.
What Are Contact Approval Systems?
Unlike traditional email filters that rely on analyzing message content, Contact Approval Systems focus on verifying the sender's identity. Think of it as a secure ID check at an exclusive event - only verified individuals are allowed in. Instead of guessing whether an email might be harmful, these systems determine exactly who sent it before letting it through.
This shift from probabilistic filtering to deterministic identity verification is critical. Why? Because attacks like Business Email Compromise (BEC), where scammers pose as trusted contacts, caused $2.8 billion in losses in 2024 alone. These attacks are tricky - they often don’t include malware or suspicious links, making traditional filters ineffective. Deterministic verification steps in to address this gap.
"Email's authentication gap has persisted for 50 years. With AI-powered attacks evolving faster than defenses, that gap is growing. Outtake Verify closes it - deterministically, privately, and without disrupting your operations."
_ - Outtake.ai_
How Contact Approval Systems Work
These systems tie the sender's identity to a physical device or secure authentication method, like a passkey or biometric verification. When someone sends an email, the system cryptographically signs the message using authentication linked to their device. Even if attackers steal login credentials, they can’t replicate this signature without the physical device.
A trust request workflow often comes into play when dealing with new senders. For instance, if you receive an email from someone unfamiliar, the system might prompt them to verify their identity through a secure handshake - like exchanging short codes over a phone call or in person. Once verified, they’re added to your approved contact list. Future emails from them display a "Verified" badge, which includes their name, photo, and job title.
Behind the scenes, cryptographic techniques, such as Merkle Trees, ensure tamper-proof verification. The email content is hashed directly on the sender's device, creating a secure record without exposing the raw content to the service provider. This process not only guarantees the email wasn’t altered during transit but also safeguards privacy.
This thorough authentication process delivers powerful security benefits.
Main Benefits of Contact Approval Systems
The standout benefit is stopping spoofing and impersonation attacks. Since these systems require cryptographic proof tied to a verified device, attackers can’t pull off traditional tricks like domain spoofing or using look-alike domains. Even if someone hacks into an email account, they can’t send "verified" emails without the physical authentication device. This makes it a more reliable defense compared to older filtering methods.
Another advantage is reducing the false positive problem. Instead of legitimate emails being misclassified as spam, recipients see clear trust signals - like "Verified" badges - indicating the sender's identity has been authenticated. Studies show these visual indicators can cut the click-through rate on spoofed emails from 48.9% to 37.2%. It also saves users time by ensuring their inbox contains emails they can trust, without the hassle of sifting through spam folders.
Traditional Email Filters vs Contact Approval Systems
This section dives into how traditional email filters and Contact Approval Systems stack up against each other. The differences aren’t just technical - they reshape how organizations approach email security and handle external communications.
Phishing Attack Prevention
Traditional email filters focus on catching threats using tools like signatures, reputation scores, and blocklists. They’re highly effective at stopping spam, blocking over 99.9% with a false positive rate below 0.01%. However, they run into issues with zero-day attacks because they depend on pre-existing threat signatures.
Contact Approval Systems take a completely different path. They build identity profiles for users and vendors, monitoring typical communication patterns. If something seems off - like an unusual request for a wire transfer or an abrupt change in tone - the system flags it, even if the email passes technical authentication checks. This makes them especially effective against business email compromise (BEC) attacks, which caused $2.77 billion in damages across 21,442 incidents in 2024. A KnowBe4 Defend study revealed that 50.72% of phishing emails bypassed either Secure Email Gateways or Microsoft 365 over a two-week period in 2023.
"Authentication protocols verify technical headers but don't authorize legitimate business communication."
_ - Abnormal AI_
Here’s a quick comparison of the two systems:
| Feature | Traditional Email Filters | Contact Approval Systems |
|---|---|---|
| Primary Detection | Signatures, reputation, blocklists | Identity-based behavioral analysis |
| BEC Protection | Limited - may miss text-only social engineering | Strong - detects language and intent anomalies |
| Zero-Day Threats | Reactive - needs known threat signatures | Proactive - flags unusual behavior |
| Visibility | Limited to perimeter scanning | Includes historical communication patterns |
These differences highlight how each system handles threats and why Contact Approval Systems offer a more adaptive approach to evolving risks.
Deployment and Management
Traditional email filters are usually implemented using Secure Email Gateways (SEGs), which require MX record redirection. This process can take days to complete and may cause downtime. They also demand ongoing manual updates, such as maintaining blocklists and adjusting rules.
Contact Approval Systems, on the other hand, integrate directly with platforms like Microsoft 365 or Google Workspace through APIs. This setup takes only minutes and gives immediate access to communication history. They can even monitor internal communications, helping detect lateral movement if an account is compromised.
While traditional filters need frequent manual maintenance, Contact Approval Systems continuously learn from your organization’s communication habits. That said, they still require occasional audits - experts recommend reviewing approved contact lists every 90 days to remove outdated entries and stay compliant with regulations. These differences in deployment and management have a direct impact on reliability and ease of use.
False Positives and User Experience
One common issue with traditional email filters is their tendency to block legitimate emails - like invoices, sales leads, or vendor updates - which can frustrate users.
Contact Approval Systems address this by analyzing the relationship history behind each message instead of relying on standalone signals. Instead of outright blocking suspicious emails, they often use dynamic warning banners to provide context, helping users stay productive.
However, there is a trade-off. Contact Approval Systems require an initial setup phase where users approve legitimate contacts through trust requests. Once this process is complete, the system runs more smoothly, though some fine-tuning might still be needed during the early stages.
Strengths and Weaknesses
Both traditional email filters and Contact Approval Systems offer distinct benefits, but they also come with trade-offs that influence how organizations manage email security on a daily basis.
Strengths of Traditional Email Filters
Traditional email filters are known for their scalability and layered defense mechanisms. Cloud-based filtering systems utilize global data centers to handle large email volumes efficiently, even as organizations grow. Vendors often report spam and phishing detection rates exceeding 99%. These systems combine multiple techniques - such as sender reputation checks, cryptographic authentication protocols like SPF, DKIM, and DMARC, content analysis, and real-time link sandboxing - to detect and block threats before they reach user inboxes.
"Effective email filtering blends authentication protocols, cloud-scale telemetry, and machine learning, with fast response when attackers change tactics."
- MaK Ulac, Guardian Digital
Another key advantage is ease of use. Automated triage eliminates the need for users to manually sort through spam, while centralized dashboards enable administrators to efficiently enforce global policies. Traditional filters also integrate seamlessly with both legacy on-premise servers and modern platforms like Microsoft 365 and Google Workspace.
Strengths of Contact Approval Systems
Contact Approval Systems shine in their ability to block sophisticated attacks. By focusing on verifying the sender's identity rather than just analyzing email content, these systems can thwart threats that bypass traditional authentication checks. This capability is particularly crucial for combating Business Email Compromise (BEC) attacks, which caused $2.77 billion in damages across 21,442 incidents in 2024.
Their zero-trust approach is another standout feature. By default, these systems block any sender that hasn’t been explicitly approved, making them highly effective against new and evolving threats, including payload-less attacks - emails without malicious links or attachments - that traditional filters might overlook. Additionally, maintaining a trusted list of known contacts helps reduce false positives for important communications, such as password resets or vendor invoices.
Weaknesses of Both Systems
Despite their strengths, both systems face challenges that can disrupt daily operations. Traditional email filters often fall short when dealing with trust-based attacks. They may struggle to detect compromised accounts or identify display-name spoofing tactics used to deceive users. Static detection methods also tend to fail against advanced threats like polymorphic or AI-generated attacks that don’t match known patterns.
"Static, rule-based filters fail against threats that exploit trust instead of malicious code."
- Abnormal AI
On the other hand, Contact Approval Systems are prone to operational bottlenecks. They rely heavily on manual intervention to review quarantined messages, which can slow down processes and lead to alert fatigue. High volumes of alerts increase the risk of overlooking genuine threats. Furthermore, analyzing communication metadata and relationship patterns raises concerns about privacy and compliance with data protection regulations.
| System Type | Primary Weakness | Mitigation Strategy |
|---|---|---|
| Traditional Filters | Vulnerable to AI-driven and trust-based attacks | Deploy Behavioral AI and Relationship Graphs |
| Contact Approval | Dependency on manual review, risk of alert fatigue | Use AI-driven auto-classification and low-latency data systems |
| Both Systems | Susceptible to "Zero-Day" exploits and credential theft | Implement phishing-resistant MFA and multi-layer endpoint protection |
To improve their effectiveness, traditional filters require regular tuning - such as reviewing quarantine release rates and false positives monthly - to refine rules and enhance accuracy. Similarly, Contact Approval Systems benefit from periodic audits to remove outdated entries and address potential security gaps.
When to Use Each System
Deciding between traditional email filters and Contact Approval Systems comes down to factors like your organization's size, industry, risk exposure, and operational needs. Both systems have their strengths, and knowing when to rely on each can help you craft a defense strategy that tackles phishing and external communication risks effectively.
When to Use Traditional Email Filters
Traditional email filters shine in settings with high email traffic and limited IT resources. For small to midsize businesses, these systems are a practical choice - they're easy to set up and require minimal ongoing management. If your organization handles thousands of emails daily, including routine spam and generic phishing attempts, these filters can efficiently sort through the clutter and prevent inbox overload.
Budget-conscious organizations also appreciate traditional filters for their cost-effective protection. Modern systems can block over 99.9% of spam while maintaining a false positive rate below 0.01%, offering reliable coverage against everyday threats.
For companies with strict compliance rules around email flow, secure email gateways linked to traditional filters are a popular option. They enable pre-delivery blocking and centralized auditing, which is especially useful for regulatory oversight. Additionally, if your infrastructure relies on older on-premises mail servers or the built-in protections of platforms like Microsoft 365 or Google Workspace, traditional filters can serve as a crucial first line of defense. However, for more targeted and sophisticated threats, a different approach may be necessary.
When to Use Contact Approval Systems
Contact Approval Systems are particularly valuable in high-risk environments where sensitive communications or financial transactions are routine. Industries like finance, healthcare, and law are prime targets for Business Email Compromise (BEC) attacks, which often evade traditional filters by using legitimate infrastructure and avoiding malicious links or attachments.
"Behavioral analysis catches text-only BEC attacks and compromised vendor emails that pass all other checks - addressing the fundamental gap in traditional filtering."
- Abnormal AI
Executives, finance teams, and other high-risk roles are frequent targets for spear-phishing and identity-based attacks. Contact Approval Systems use behavioral baselines to spot anomalies and detect zero-day threats that traditional filters might overlook. Considering that 90% of cyberattacks start with phishing emails and AI-generated phishing attempts are nearly as convincing as human-crafted ones, the zero-trust model of Contact Approval Systems becomes a critical layer of defense.
These systems are most effective in tightly controlled environments where the list of approved contacts is small and well-defined, such as internal databases or secure customer portals. If your team frequently deals with wire transfers, protected health information, or sensitive legal documents, the added step of manual verification - though requiring more effort - can significantly reduce the risk of major security breaches.
Why Eleidon Stands Out as a Contact Approval System
In the world of email security, Eleidon addresses the gaps left by traditional filters. These older systems struggle with challenges like a 22.5% annual decay rate in B2B email data and up to 30% of enterprise contacts falling into verification gray zones. Eleidon takes a fresh approach by embedding security directly into the communication process, moving away from methods that depend solely on content scanning or blacklists.
Here’s a closer look at Eleidon’s design and how it supports secure communication.
Key Features of Eleidon
Eleidon employs cryptographic sender verification to confirm a sender's identity without question. This approach eliminates the uncertainty that can arise when Secure Email Gateways obscure SMTP handshakes.
The system also uses end-to-end encryption (E2EE) within a zero-knowledge framework. This ensures that messages are secure from the moment they’re sent until they’re received, and even Eleidon itself cannot access the content. This level of security is especially critical, given that phishing accounts for 72% of social engineering attacks and played a role in 22% of data breaches between 2013 and 2016.
For businesses, Eleidon offers centralized team management, enabling administrators to enforce secure communication protocols across the organization without dealing with complicated setups. It also features a trust request system that allows users to control who can contact them. This reduces alert fatigue and eliminates the need for manual triage.
These technical strengths are paired with simple pricing plans, making Eleidon accessible and practical for enterprises.
Pricing and Plans
Eleidon keeps its pricing straightforward with three tiers for personal, team, and enterprise use.
- The Personal plan is free forever and includes an @eleidon email address, unlimited encrypted messages, and access across multiple devices.
- The Team plan, priced at $9 per user per month, adds features like custom domain support, centralized team management, and priority customer support.
- For organizations needing enhanced recovery options, the Team + Vault plan costs $14 per user per month. It includes encrypted key backup, multi-device sync, and an account recovery guarantee, along with all features from the Team plan.
These pricing options and features make Eleidon a seamless choice for deploying and managing Contact Approval Systems, reinforcing the advantages discussed earlier.
Conclusion
Deciding between Traditional Email Filters and Contact Approval Systems hinges on what your organization needs most. Traditional filters are great at blocking bulk spam and known malware, acting as an automated first line of defense. But they fall short when it comes to advanced threats like Business Email Compromise (BEC) attacks - which have caused over $50 billion in global losses - and newer tactics, such as AI-generated phishing, that evade signature-based detection.
On the other hand, Contact Approval Systems focus on verifying the sender's identity before emails reach your inbox. This approach addresses the staggering fact that 90% of cyberattacks start with phishing emails, and it takes an average of 295 days to detect and stop phishing attacks with traditional methods. By eliminating reliance on content scanning, these systems reduce uncertainty and provide clear audit trails, making them particularly effective for high-stakes communication.
For organizations, a combination of both systems offers a well-rounded strategy. Traditional filters act as the first layer of defense, while Contact Approval Systems are better suited for sensitive communications and critical client interactions. Industries like legal, healthcare, and financial services - where confidentiality is non-negotiable - stand to gain from the accountability these systems bring.
Eleidon is a standout example of this modern approach, offering cryptographic verification and end-to-end encryption. With pricing starting at $9 per user per month for teams, Eleidon combines enterprise-grade security with simplicity. Its trust request system and centralized management tools are designed to handle the increased risk, especially with phishing attacks surging by 147% between 2023 and 2024. This makes it an excellent fit for organizations that can't afford to take chances.
Ultimately, the right choice depends on your risk tolerance, collaboration requirements, and the potential financial impact of a breach. For environments where the average cost of a security incident is $4.88 million, Eleidon’s proactive Contact Approval System provides a level of protection that traditional filters alone simply can't match.
FAQs
Do I need both email filters and a Contact Approval System?
Using both tools together can boost your email security since they tackle different challenges. Email filters are great for blocking spam, malware, and other known threats. However, more sophisticated attacks, like phishing, can sometimes slip through. That’s where a Contact Approval System comes in - it adds an extra layer of defense by requiring explicit approval for external communications, making it harder for targeted attacks to succeed. While it's not a requirement to use both, combining them addresses a broader range of vulnerabilities and strengthens your overall protection.
How does a Contact Approval System verify a sender if an account gets hacked?
A Contact Approval System works by verifying senders through risk-based approval policies, identifying unusual behavior, and enhancing sender verification to spot irregularities. These steps ensure that even if an account seems legitimate, any compromised activity is flagged, preventing misplaced trust.
What’s the best way to roll out contact approvals without slowing teams down?
Automated workflows are a smart way to streamline processes while maintaining control. By integrating them smoothly into your current systems, you can handle routine approvals automatically, saving time and effort. For higher-risk contacts, these workflows can flag them for manual review, ensuring nothing slips through the cracks.
Establishing clear rules is key. With well-defined guidelines, low-risk cases can be approved quickly, avoiding unnecessary delays. This approach strikes a balance between efficiency and oversight, keeping things moving without sacrificing accuracy or control.