
5 Data Breach Prevention Strategies for IT Teams
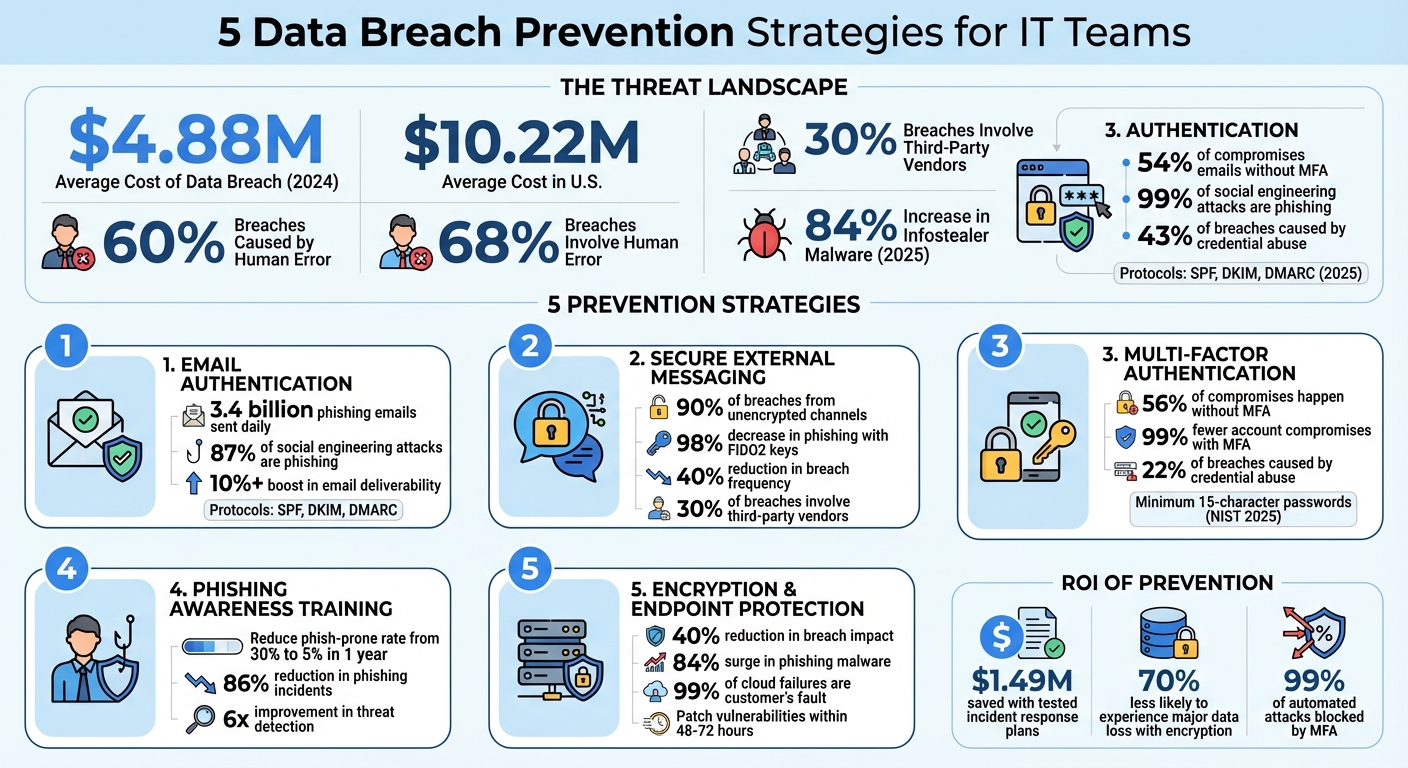
Data breaches are becoming more frequent and costly, with phishing and credential theft leading the charge. In 2024, human error caused 60% of breaches, while stolen credentials contributed to nearly one-third. The average cost of a breach hit $4.88 million, making it clear that traditional defenses are no longer sufficient. Attackers are now bypassing multi-factor authentication (MFA) and exploiting session cookies, further complicating the landscape.
To counter these threats, here are five proven strategies for IT teams:
- Email Authentication: Use SPF, DKIM, and DMARC protocols to block phishing and domain spoofing.
- Secure External Messaging: Encrypt communications and verify sender authenticity to protect data shared externally.
- Phishing-Resistant MFA: Replace weak methods like SMS codes with FIDO2 hardware keys or passkeys.
- Awareness Training: Conduct phishing simulations and teach employees to recognize and report threats.
- Encryption & Endpoint Protection: Encrypt sensitive data and deploy tools to detect and block malware.
These measures address modern threats like AI-driven phishing, infostealer malware, and session hijacking, while also helping organizations meet compliance requirements like GDPR and HIPAA. By layering these defenses, IT teams can significantly reduce the risk of breaches and their associated costs.
Data Breach Statistics and Prevention Strategies 2024-2025
15 Years of Breach Response: These 5 Controls Actually Work
sbb-itb-804866a
1. Set Up Email Authentication Protocols
Email authentication is your first line of defense against data breaches, phishing, and spoofing. Protocols like SPF, DKIM, and DMARC work together to verify sender identities and ensure email integrity. Here's how they function:
- SPF (Sender Policy Framework): Acts as a whitelist in your DNS, specifying which servers are authorized to send emails on your domain's behalf.
- DKIM (DomainKeys Identified Mail): Uses cryptographic signatures to confirm the integrity of your email content.
- DMARC (Domain-based Message Authentication, Reporting & Conformance): Combines SPF and DKIM, ensuring alignment between the visible "From" address and authenticated domains. It also directs email receivers on how to handle messages that fail authentication (deliver, quarantine, or reject).
Effectiveness in Preventing Phishing and Data Breaches
Phishing attacks often exploit domain spoofing, which email authentication can effectively block. With 3.4 billion phishing emails sent daily and phishing responsible for 87% of social engineering attacks, the stakes are high. Red Sift highlights the importance of DMARC in combating these threats:
"DMARC at p=reject is the most effective control for stopping domain spoofing and brand impersonation at scale".
Adopting a p=reject DMARC policy not only thwarts phishing attempts but can also boost email deliverability by over 10% due to improved sender reputation. This is critical, especially when AI-driven Business Email Compromise (BEC) scams cause average losses of $150,000 per incident. These measures also make it easier to meet regulatory requirements.
Ease of Implementation for IT Teams
Setting up email authentication can be straightforward if approached methodically:
- Inventory email-sending platforms: Include tools like Google Workspace, Microsoft 365, CRMs, and marketing services.
- SPF setup: Create a single SPF DNS TXT record that lists authorized IP addresses. Keep SPF lookups under 10 to avoid issues.
- DKIM configuration: Generate 2048-bit RSA key pairs for each sending service. Each provider needs a unique selector and public key stored in DNS.
- DMARC rollout: Begin with
p=noneto monitor reports, then move top=quarantineand finallyp=rejectonce all legitimate senders are verified.
For verification, tools like Gmail’s "Show Original" feature can confirm spf=pass, dkim=pass, and dmarc=pass before enforcement. Regular maintenance, such as rotating DKIM keys every six to twelve months and conducting quarterly DNS audits, ensures continued effectiveness.
Compliance with Industry Standards and Regulations
Email authentication plays a key role in meeting data protection regulations like GDPR and HIPAA by preventing unauthorized access to sensitive information. For U.S. government agencies, DMARC enforcement at p=reject is mandated under CISA Binding Operational Directive 18-01.
Additionally, major email providers like Google and Yahoo require SPF, DKIM, and at least a p=none DMARC policy for bulk senders (over 5,000 emails daily) starting February 2024. For enhanced security, consider implementing MTA-STS to enforce TLS encryption and block downgrade attacks.
2. Use Secure External Messaging with Cryptographic Verification
When communicating with vendors, clients, or partners through external messaging platforms, the absence of cryptographic verification can leave data exposed. Considering that 90% of data breaches result from unencrypted communication channels, securing these platforms is essential.
Effectiveness in Preventing Phishing and Data Breaches
Cryptographic verification transforms vulnerable communication channels into secure ones by using end-to-end encryption (E2EE). This ensures messages are encrypted at the source and decrypted only at their intended destination. With phishing attacks becoming increasingly sophisticated - often driven by AI - such measures are no longer optional but necessary.
Passkeys and FIDO2 technology further enhance protection by replacing traditional passwords with device-stored cryptographic keys. This approach ensures that even if a user interacts with a fraudulent site, no reusable credentials are at risk. The results speak for themselves: users employing FIDO2 hardware keys or biometric passkeys experienced a 98% decrease in successful phishing attempts. Messaging platforms that incorporate DKIM and DMARC protocols add an additional layer of protection by verifying sender authenticity.
These encryption-based safeguards directly counter evolving threats that exploit unprotected channels, creating a strong foundation for implementing secure external messaging practices.
Ease of Implementation for IT Teams
IT teams can streamline the adoption of secure messaging by phasing out outdated protocols. Start by disabling protocols like POP3 and IMAP, which rely on "Basic Authentication" and are vulnerable to modern attacks. Transition to phishing-resistant multi-factor authentication (MFA) methods, such as FIDO2 hardware security keys or passkeys, which utilize origin-bound cryptographic signatures.
For high-risk communications, such as financial transactions or sensitive data changes, use out-of-band verification through a secondary channel like an encrypted chat or phone call to confirm authenticity. Additionally, enable "External Guest" banners on messaging platforms to visually indicate when non-internal participants are part of a secure conversation. Regularly review and audit third-party app OAuth permissions to remove unnecessary access to external messaging data.
Compliance with Industry Standards and Regulations
Cryptographic verification isn't just a best practice - it’s often a legal requirement under frameworks like GDPR and HIPAA. For example, breaches in the healthcare sector, regulated under HIPAA, average $7.42 million in remediation costs. GDPR violations can lead to fines of up to 4% of an organization’s annual global revenue.
Consumer messaging apps like WhatsApp and Signal lack the necessary access controls and audit trails for compliance. In contrast, enterprise-grade platforms offer features like role-based access control, auditable records, and metadata protection - critical for meeting regulatory standards. As Wire highlights:
"Secure internal communication can no longer be treated just as a compliance checkbox. It is a strategic differentiator and advantage that builds trust, resilience and operational excellence".
Scalability for Enterprise Environments
For large organizations, Messaging Layer Security (MLS) is emerging as a vital tool, bringing E2EE to large-scale group messaging without compromising security, regardless of the number of participants. This is particularly important as 30% of breaches last year involved third-party vendors - a figure that has doubled since 2024.
Organizations that adopt strong encryption practices report a 40% reduction in the frequency and impact of data breaches. To scale securely, enterprises can segment communication channels, creating separate cryptographically protected spaces for internal teams and external partners. Sensitivity labels can further enhance security by automatically encrypting messages containing personal or health-related information and restricting their forwarding.
Strengthening the security of external communications is a key step in a broader strategy to prevent data breaches effectively.
3. Require Multi-Factor Authentication and Strong Passwords
Effectiveness in Preventing Phishing and Data Breaches
The numbers speak volumes: in Q1 2025, 56% of security compromises happened without multi-factor authentication (MFA), highlighting that relying on passwords alone just doesn’t cut it anymore. Credential abuse caused 22% of breaches that same year, making it clear that stronger measures are needed.
MFA adds an extra layer of defense by requiring two or more verification factors - like something you know (your password), something you have (a token or your phone), or something you are (biometrics). This approach makes unauthorized access much harder. Organizations using MFA report up to 99% fewer account compromises compared to systems relying on passwords alone.
However, not all MFA methods are equally secure. SMS and email-based one-time passwords, for example, are vulnerable to attacks like SIM swapping or MFA fatigue. More secure options, such as phishing-resistant MFA using protocols like FIDO2, WebAuthn, or passkeys, use cryptographic origin binding to ensure authentication only works on legitimate domains. As CyberDesserts puts it:
"MFA remains the single most effective control against credential-based attacks".
Given the 84% rise in infostealer malware in 2025, basic password policies without phishing-resistant MFA leave organizations exposed. Implementing MFA as part of a layered security strategy is a must.
Ease of Implementation for IT Teams
For IT teams, setting up basic MFA - like time-based one-time passwords (TOTP) or push notifications - can be done in just 30–60 minutes for initial deployment. However, testing for edge cases and integrating with legacy systems may require additional effort. A good starting point is to secure high-risk accounts with FIDO2 hardware keys. Scaling this across the organization becomes easier by centralizing MFA through an Identity Provider (IdP), which ensures consistent enforcement of policies across cloud apps, VPNs, and on-premise systems.
Adaptive MFA adds another layer of usability by triggering extra verification only in unusual situations, such as logins from unexpected locations or devices. This strikes a balance between security and convenience, even for large user bases.
Strong password policies are another critical piece of the puzzle. Following NIST SP 800-63B Rev. 4 (August 2025), organizations should enforce passwords with a minimum of 15 characters. Avoid requiring regular password changes unless a breach occurs. Using enterprise password managers can centralize credential management, enforce access controls, and flag weak or reused passwords. Regular privilege reviews - every 90 days - help identify and remove orphan accounts or prevent privilege creep as employees change roles. Centralizing MFA not only simplifies the rollout but also supports compliance efforts.
Compliance with Industry Standards and Regulations
MFA isn’t just a good idea - it’s a requirement under regulations like HIPAA, PCI DSS, GDPR, and SOC 2. While HIPAA doesn’t specify password length, it does call for "reasonable and appropriate" safeguards. Aligning with NIST 2025 standards can help meet these expectations. Similarly, GDPR mandates strong technical and organizational measures, and implementing MFA with encryption ticks those boxes.
The stakes are high. In 2024, the global average cost of a data breach hit $4.88 million, while in the U.S., it soared to $9.36 million. With 91% of breaches starting from spear-phishing emails, combining MFA with strong password policies is essential - not just for compliance but also for reducing risk. Paired with tools like secure messaging and encryption, these measures form a solid defense against advanced threats.
Scalability for Enterprise Environments
Single sign-on (SSO) simplifies authentication, making it easier to enforce robust MFA across a wide range of systems. Adaptive MFA scales well, ensuring smooth access for most users while adding extra verification for high-risk scenarios. Despite workforce MFA adoption reaching 70% in 2025, the remaining 30% still leaves room for breaches. Closing this gap means enforcing MFA for all users - not just admins. Attackers often exploit standard user accounts for lateral movement.
Account recovery workflows should also include step-up verification or admin approval for high-privilege resets to avoid bypassing MFA. Automating offboarding processes ensures accounts are promptly disabled when employees leave. As miniOrange warns:
"Implementing MFA poorly creates a false sense of security that's arguably worse than having no policy at all".
For today’s threat landscape, combining phishing-resistant MFA with strong password policies isn’t optional - it’s essential.
4. Run Phishing Awareness Training and Simulations
Effectiveness in Preventing Phishing and Data Breaches
While firewalls and antivirus software are essential, they can't fully protect against the human element of cyberattacks. With social engineering playing a role in 70% to 90% of breaches, phishing awareness training is a must. Organizations that consistently train their employees can slash their "phish-prone" rates from over 30% to just 5% in a year. Beyond that, training helps employees recognize and report threats, leading to a sixfold improvement in detection within six months and cutting phishing incidents by 86%.
But success isn't just about lowering click rates. Modern training programs focus on metrics like reporting speed (TTR) and the percentage of incidents reported. These indicators help limit the time attackers have to exploit a breach. Maxime Cartier, Head of Human Risk at Hoxhunt, highlights the importance of this approach:
"Click rate never goes down to zero... and focusing on click rates means we focus on failure. That can be really damaging to psychological safety - people become afraid to report mistakes."
Phishing tactics have also evolved. Attackers now use SMS (smishing), voice calls (vishing), and QR codes (quishing) to bypass traditional defenses [36,37]. Training simulations should reflect these multi-channel threats, especially since 68% of breaches involve human error. By mirroring real-world scenarios, employees can better prepare for attacks.
To make these benefits a reality, IT teams should integrate automated training modules into their workflows, ensuring consistent and effective education.
Ease of Implementation for IT Teams
Modern training platforms make life easier for IT teams by integrating seamlessly with tools like Microsoft 365, Google Workspace, and Slack. Automation handles much of the heavy lifting, while adaptive difficulty adjusts simulation frequency based on risk levels [43,39,42]. Features like a "Report Phish" button - available as an add-in for Outlook or Gmail - streamline reporting and reinforce good habits [38,39]. If an employee falls for a simulation, an immediate "Oops" landing page and a quick 90-second micro-lesson help them learn from the mistake while it's fresh [36,38,42].
To ensure accurate metrics, whitelist your simulation provider in tools like Microsoft Defender. Automated link scanners can click on simulation links before employees do, skewing results and potentially triggering unnecessary follow-ups [36,38]. High-risk roles, such as those in Finance, IT, or Executive Support, should receive more frequent and tailored micro-drills [36,38,39]. Platforms with AI-driven automation can also adjust content and training schedules based on user risk profiles, reducing the administrative load for IT teams [39,42].
These tools and strategies make it possible to run a scalable and effective training program without overwhelming your team.
Compliance with Industry Standards and Regulations
Phishing simulations aren't just good practice - they're often required. They align with GDPR, HIPAA, SOC 2, ISO 27001, and PCI DSS standards [36,42]. Automated reporting provides detailed analytics on click rates, credential entry, and response times, creating a reliable audit trail [42,44]. Companies with strong training programs have even reduced their average breach costs by $950,000 per incident.
Under GDPR, simulations typically fall under the "legitimate interests" legal basis, as long as organizations document a Legitimate Interest Assessment (LIA) and implement safeguards. This approach demonstrates due diligence and can help avoid regulatory fines [6,42].
Scalability for Enterprise Environments
AI-powered platforms can scale to meet the needs of global enterprises, offering multi-language support and personalized training for different departments [36,42,43]. For example, Finance teams might receive invoice-themed phishing simulations, while IT teams face SSO-reset scenarios [36,37]. New hires are especially vulnerable - 44% are more likely to click malicious links, and 71% are more susceptible to social engineering in their first three months. Including targeted training during onboarding is essential.
To keep employees engaged without overwhelming them, aim for one simulation per month [36,37,38]. Advanced platforms can also feed simulation data into the Security Operations Center (SOC), helping stress-test your organization’s response protocols. Avoid punishing employees for repeated mistakes; instead, use positive reinforcement, gamification (like leaderboards and badges), and one-on-one coaching to foster a culture of security [38,39].
As James Briscoe from Hoxhunt puts it:
"The challenge isn't awareness - the challenge is execution. People are busy, switching contexts, focused on their own domain. They're not in a secure mindset when the risky moment hits."
Building that secure mindset takes ongoing, realistic training tailored to your organization’s needs.
5. Apply Advanced Encryption and Endpoint Protection
Effectiveness in Preventing Phishing and Data Breaches
Encryption plays a key role in protecting data, whether it's stored on hard drives, cloud databases, or backups, or being transmitted via email, API calls, or file uploads. It reduces the impact of breaches by 40%, potentially saving millions compared to the average breach cost of $10.22 million. Even if attackers manage to access the network, encrypted data is useless without the decryption key.
Endpoint protection tools add another layer of security by monitoring user behavior in real time and stopping infostealer malware before it can steal credentials. This is especially important as phishing attacks delivering malware have surged by 84%, with 30% of compromised systems being enterprise-managed devices. Solutions like Extended Detection and Response (EDR/XDR) analyze data from endpoints, servers, and cloud environments to block threats in real time. This is crucial since human error contributes to approximately 60% of data breaches.
"Encryption is your last line of defense. It protects data when other controls fail." - Josh Amishav
Cloud-based tools make it easier than ever to deploy encryption and endpoint protection, streamlining implementation for organizations.
Ease of Implementation for IT Teams
Advanced encryption and endpoint protection measures are not only effective but also relatively simple to implement. Cloud platforms such as Microsoft Azure and AWS offer built-in tools for Full Disk Encryption (FDE) on virtual machines and storage buckets. For data in transit, TLS 1.3 with Perfect Forward Secrecy ensures secure communication. Unified management platforms allow IT teams to enforce security policies across multiple environments - cloud, web, email, and endpoints - while context-sensitive Data Loss Prevention (DLP) tools adjust controls based on the sensitivity of the data and user roles, minimizing disruptions.
A phased rollout can make adoption smoother. For instance, starting endpoint protection in "log-only" mode allows IT teams to monitor normal behavior before activating blocking features, reducing the risk of employee frustration or unsafe workarounds. Automation also plays a big role: patching critical vulnerabilities within 48 to 72 hours - far faster than the median patch time of 32 days - can significantly reduce risks, as vulnerabilities account for 20% of breaches. Automated tools can also scan endpoints for sensitive data, like PII or intellectual property, that may be stored locally without proper authorization.
Compliance with Industry Standards and Regulations
Encryption is essential for meeting regulatory requirements such as GDPR, HIPAA, PCI DSS, SOC 2, and ISO 27001. For example, GDPR Article 32 requires "appropriate technical and organisational measures", while HIPAA mandates encryption or an equivalent safeguard.
Failing to comply with these standards can lead to severe penalties. GDPR violations can incur fines of up to €20 million or 4% of global annual revenue, whichever is higher. HIPAA violations for repeat offenses can result in fines of up to $1.5 million annually. A notable example: the University of Rochester Medical Center paid $3 million in 2019 after losing an unencrypted laptop and USB drive. Gartner has highlighted that "through 2025, 99% of cloud security failures will be the customer's fault", often due to misconfigurations. Robust encryption, such as AES 256-bit for storage and TLS 1.3 for data in transit, can help address these risks while ensuring compliance.
Scalability for Enterprise Environments
Encryption and endpoint protection solutions are designed to scale across large enterprises, integrating seamlessly with broader security frameworks. AI-powered DLP systems, for instance, can continuously scan and classify massive amounts of data. Platforms like IBM Z offer "pervasive encryption", simplifying the process of protecting all data at rest and in transit.
Unified Endpoint Management (UEM) and Mobile Device Management (MDM) platforms further enhance scalability. These tools allow IT teams to enforce multi-factor authentication, push patches, and even remotely wipe lost or stolen devices - all from a central console. This is particularly critical as non-human identities, such as service accounts and APIs, now outnumber human users by an astonishing 82 to 1. Prioritizing privileged accounts for advanced protections, like FIDO credentials (passkeys), ensures that the most sensitive accounts are safeguarded first. Additionally, maintaining an up-to-date inventory of technology assets - at least annually - helps ensure that every device accessing sensitive data is accounted for.
"Security that reads well on paper but fails during an incident is a liability. Build your program once, operate it daily, and let compliance follow." - Amit Gupta, Founder & CEO of Konfirmity
Conclusion
Preventing data breaches isn't about finding a single, flawless solution. It's about layering defenses so that when one measure falters, others step in to mitigate the damage. For example, email authentication stops spoofed messages before they hit inboxes, while multi-factor authentication (MFA) renders stolen passwords useless. Meanwhile, employee training transforms your workforce from a potential weak spot into a strong line of defense. And if attackers do manage to break through, encryption ensures that stolen data remains unreadable and essentially useless.
The statistics underscore the importance of these measures: the average data breach in the U.S. costs $10.22 million. However, organizations with tested incident response plans can save an average of $1.49 million in breach-related costs. MFA alone blocks over 99% of automated credential-based attacks, and companies that consistently apply encryption are 70% less likely to experience major data loss during a breach.
No single method can address every threat. While technical controls like endpoint protection and encryption are crucial, the human factor plays a role in about 60% of all data breaches. This is why phishing simulations and awareness training are just as critical as firewalls or encryption keys. Regulatory compliance then ties these efforts together, ensuring that your organization maintains a strong baseline of protections and clear response protocols.
"Effective data breach prevention begins with the realization that you need a blended approach of proven techniques – one technique, tool, or strategy won’t suffice on its own, no matter how powerful." - Zoran Cocoara, Endpoint Protector
Start with the essentials: enforce MFA on all accounts, conduct quarterly phishing simulations, and apply critical patches within 72 hours of release. Follow the 3-2-1 backup rule - three copies of your data on two types of media, with one stored off-site. Above all, treat security as a continuous effort, not a one-time task. The threat landscape changes daily, and your defenses must adapt just as quickly.
FAQs
Which three controls should we implement first for the biggest risk reduction?
To tackle risks swiftly, focus on these three key actions:
- Turn on multi-factor authentication (MFA): This adds an extra layer of security, stopping unauthorized access even if someone has stolen login details.
- Keep an eye on credentials: Use proactive monitoring methods, like dark web surveillance, to spot stolen data before it becomes a problem.
- Protect external communication and cloud setups: Ensure cloud configurations are secure and communication channels are properly safeguarded to avoid leaks and missteps.
These measures target frequent vulnerabilities and help reduce the likelihood of breaches.
How do we roll out DMARC to p=reject without breaking legitimate email?
To apply DMARC with p=reject safely, it’s best to take a step-by-step approach. Begin by identifying all legitimate email senders associated with your domain. Set up SPF and DKIM for each sender to ensure proper authentication. Next, configure DMARC with a p=none policy and enable full reporting using the rua (aggregate reports) and ruf (forensic reports) tags.
Carefully review the reports to identify any misconfigurations or unauthorized senders. Once everything is aligned, gradually increase enforcement by transitioning to p=quarantine and eventually to p=reject. Use the pct tag to apply the policy incrementally, allowing you to test the waters without fully committing at once.
Throughout this process, ensure SPF and DKIM alignment. If your emails are forwarded, consider implementing ARC (Authenticated Received Chain) or SRS (Sender Rewriting Scheme) to reduce the risk of legitimate messages being blocked. This methodical rollout minimizes disruptions while strengthening your email security.
What’s the simplest way to move from SMS MFA to phishing-resistant passkeys?
To simplify the shift to stronger security, start by implementing a passkey-first authentication system. This means prioritizing WebAuthn/FIDO2 passkeys as the primary method for logging in. You can phase out SMS-based multi-factor authentication (MFA) by configuring your identity provider to favor passkeys for user verification and requiring them across all access points. This approach aligns with recommendations from trusted organizations like CISA and the FIDO Alliance, ensuring a smoother move to a phishing-resistant authentication system.