
Ultimate Guide to Encryption Key Backup Systems
Encryption key backup systems are critical for safeguarding sensitive data. Losing encryption keys can result in permanent data loss, making secure backups indispensable. These systems use techniques like envelope encryption to protect keys and ensure recoverability even during disasters. Here's what you need to know:
- How It Works: A Data Encryption Key (DEK) encrypts your data, while a Key Encryption Key (KEK) protects the DEK. This layered approach ensures security even if backups are compromised.
- Why It Matters: Without backups, lost keys lead to irretrievable data. Backups also help meet regulatory requirements like HIPAA, PCI DSS, and NIST SP 800-57.
- Who Needs It: Industries like finance, healthcare, government, and IT rely on encryption key backups to secure data and meet compliance standards.
- Key Practices:
- Use Hardware Security Modules (HSMs) or cloud-based Key Management Services (KMS) for secure key handling.
- Rotate keys regularly to reduce exposure risks.
- Store backups in multiple secure locations with redundancy.
- Implement safeguards like multi-factor authentication (MFA), soft-delete periods, and M-of-N schemes for added protection.
Proper encryption key management ensures data remains accessible and secure, even in the face of hardware failures, accidental deletions, or cyberattacks.
Encryption Key Management Explained Simply
sbb-itb-804866a
Understanding the Key Lifecycle in Backup Systems
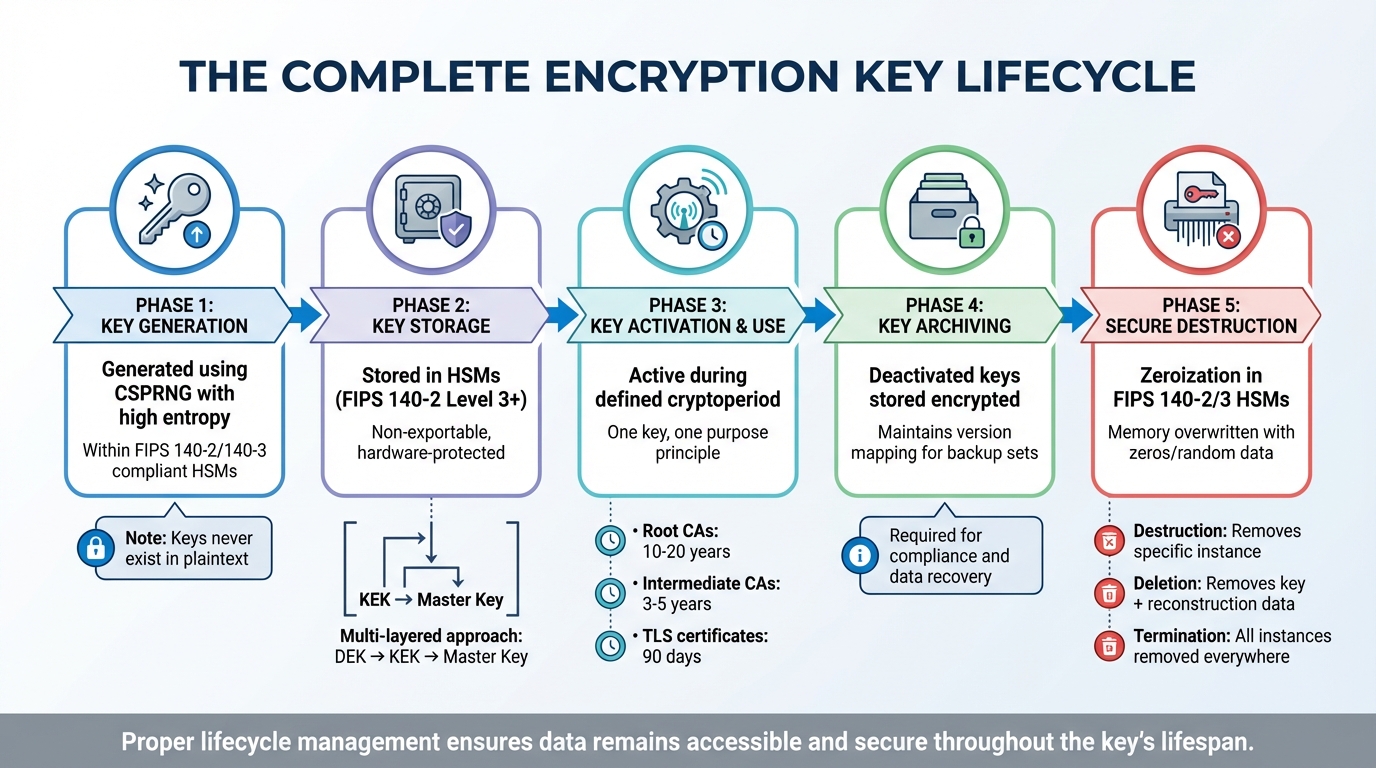
Encryption Key Lifecycle: From Generation to Secure Destruction
Key Generation and Storage
Encryption keys must be created with care, using Cryptographically Secure Random Number Generators (CSPRNG) that provide high entropy. This process should occur within hardware modules compliant with FIPS 140-2 or 140-3 standards. If keys are predictable, even strong encryption like AES-256 can be bypassed without breaking the algorithm itself.
Once created, keys should never exist in plaintext. The best practice is to use Hardware Security Modules (HSMs) certified to FIPS 140-2 Level 3 or higher. These modules ensure keys are non-exportable. To reduce risks, backup systems adopt a multi-layered approach, generating keys directly within the backup management module (whether it's an HSM or Key Management System) to avoid exposure during transit.
Key Activation, Archiving, and Expiration
Every key has a defined cryptoperiod, a set timeframe during which it can be used. Using a key beyond this period increases the chances of exposure or cryptanalysis. According to NIST guidelines, the rotation frequency depends on the key's use: Root Certificate Authorities should rotate every 10–20 years, Intermediate CAs every 3–5 years, and TLS certificates every 90 days.
During the active phase, adhering to the principle of "one key, one purpose" limits potential damage in case of compromise. Once deactivated, keys move into an archiving phase, where they are securely stored in encrypted form to meet compliance and auditing requirements. This ensures that older encrypted data remains accessible if needed for legal or regulatory reasons.
Backup systems must also maintain a detailed mapping of which key version was used for each backup set. Without this mapping, restoring encrypted backups becomes impossible. This structured lifecycle supports secure key retirement, which is the next critical step.
Secure Key Destruction
After a key has served its purpose and met archiving requirements, it must be securely destroyed. This process is more involved than simply hitting "delete." FIPS 140-2/3-certified HSMs use zeroization, a method that erases key material from hardware by overwriting it when tampering is detected or a key is deleted. For software-based keys, memory buffers must be overwritten with zeros or random data.
It's important to differentiate between destruction, deletion, and termination. Destruction removes a specific key instance at one location but leaves the possibility of reconstruction from other sources. Deletion removes the key and all reconstruction data from operational storage. Termination ensures all instances of the key are removed everywhere, making regeneration impossible.
For backup systems, this involves cryptographic erasure, which verifies that all backup copies of the key have been securely deleted. Without proper zeroization, old keys could be reconstructed from memory dumps or swap files, leaving historical data exposed to potential threats.
Best Practices for Encryption Key Backup
Securing the Backup Process
Encryption key backups should always be encrypted using a Key Encryption Key (KEK) that matches or exceeds the strength of the original key. A common choice is AES-256 encryption, which offers strong protection against brute-force attacks.
To safeguard against disasters, ransomware attacks, or hardware failures, store backup copies in secure, offline locations that are geographically distinct. A stark reminder of the importance of this practice came during the Codefinger ransomware attack in January 2025, where compromised AWS credentials caused irreversible data loss due to the absence of retained key material.
For added security, consider using Shamir's Secret Sharing. This method divides a recovery key into multiple parts, or "shards", using an M-of-N scheme. For example, in a 3-of-5 setup, any three of the five designated custodians must collaborate to reconstruct the key. Access to these shards should follow the Principle of Least Privilege, with Multi-Factor Authentication (MFA) required for sensitive actions like key deletion or export. Additionally, implementing dual control - requiring at least two authorized individuals to approve critical tasks such as key rotation or recovery - offers another layer of protection.
To mitigate risks from accidental or malicious key deletions, enable a soft delete protection period, typically around 30 days. Many cloud providers include this safeguard, ensuring that keys are deactivated but not immediately destroyed.
"Adequate key management is critical; without it, even the strongest encryption fails." - OneUptime
With backups securely stored, regular key rotation and the use of ephemeral keys can further reduce exposure risks.
Key Rotation and Ephemeral Keys
Regular key rotation is essential for minimizing the risk of long-term exposure. The frequency of rotation depends on the type of key:
- Master Keys: Rotate every 1–3 years or annually.
- Key Encryption Keys (KEKs): Rotate quarterly.
- Data Encryption Keys (DEKs): Rotate frequently, such as after every backup or after processing a specific data volume.
- Session Keys: Use for temporary operations, lasting only minutes or hours.
For AES-GCM mode, keys must be rotated before encrypting approximately 2^32 blocks to avoid initialization vector collisions, which could lead to data vulnerabilities. When rotating keys, use a "rotate and retire" strategy: mark the old key as "decrypt-only" to maintain access to previously encrypted data while using the new key for future encryption.
Key rotation should also occur immediately under specific circumstances - such as when key personnel leave, after system updates, or if a breach is suspected. Automating this process through Key Management Systems (KMS) reduces the risk of human error.
Ephemeral keys, designed for short-term use, enhance security by providing Perfect Forward Secrecy. Even if a long-term key is compromised, past sessions remain secure.
"The longer a key is in use, it only increases its chances of being compromised." - GlobalSign
Cloud-Based Key Management
Cloud-based Key Management Services (KMS) offer centralized control over encryption keys with advanced security features. Hardware Security Modules (HSMs) certified to FIPS 140-2/140-3 standards ensure plaintext key material remains confined within a secure hardware boundary.
A multi-tier hierarchy is recommended for key management: wrap Data Encryption Keys (DEKs) with KEKs and protect KEKs with a Master Key stored in an HSM. This envelope encryption approach is particularly effective for encrypting large datasets, as it enhances performance while limiting the exposure of the master key.
Adding Additional Authenticated Data (AAD) during encryption binds metadata - such as department or project identifiers - to the ciphertext. This ensures decryption fails if the metadata doesn't match, further securing the data.
Cloud KMS platforms allow customizable key rotation intervals. For instance, AWS KMS supports rotation periods ranging from 90 days to approximately 7 years (2,560 days). To enhance monitoring, enable audit logs like AWS CloudTrail to track events such as key decryption, disabling, or deletion. Real-time alerts for unauthorized deletion attempts are an essential safeguard.
To reinforce security, enforce separation of duties. The individual responsible for key creation or rotation should not handle cryptographic operations. Restrict key usage by applying condition keys (e.g., kms:ViaService) to ensure keys are only accessed through authorized services. Additionally, Service Control Policies can limit deletion permissions to a designated "break-glass" role for emergencies.
The risks of poor access controls are clear. In 2024, over 39 million leaked secrets - including API keys and credentials - were found in public GitHub repositories, emphasizing the need for stringent and continuously monitored access controls.
Tools and Technologies for Key Backup
Hardware Security Modules (HSMs)
Hardware Security Modules (HSMs) are specialized devices - available in both physical and virtual forms - designed to generate, store, and safeguard cryptographic keys. They adhere to strict compliance standards, such as FIPS 140-2/3 Level 3, and come with a built-in fail-safe: any attempt to breach them results in automatic key erasure.
"HSMs are tamper-resistant devices designed so that if someone attempts to physically or logically breach them, keys are erased or otherwise protected." – Ubiq Security
Cloud providers offer both software-protected and HSM-backed key options. For instance, Google Cloud KMS provides software-protected keys validated to FIPS 140-2 Level 1 at a cost of about $0.06 per key version per month. On the other hand, Cloud HSM keys, which meet FIPS 140-2 Level 3 standards, range from $1.00 to $2.50 per key version per month. Similarly, Azure Key Vault Premium secures keys using HSM Platform 2, certified to FIPS 140-3 Level 3.
HSMs also include advanced recovery mechanisms like security domains. For example, Azure Managed HSM uses a security domain encrypted with Shamir's Secret Sharing to restore services or import backups. This method requires a quorum of RSA key pairs (e.g., 3 out of 5) for access, reducing risks from insider threats through an M-of-N authentication scheme. To avoid operational pitfalls, ensure that HSM backups do not rely on keys stored within the same HSM.
While HSMs deliver strong hardware-based security, cloud-based Key Management Services (KMS) complement them by automating key lifecycle management.
Key Management Services (KMS)
Key Management Services (KMS) are cloud-based platforms that simplify encryption workflows. They use envelope encryption - where a master key secures data keys - and automate processes like key generation, rotation, backup, and recovery. Providers such as AWS KMS, Google Cloud KMS, and Azure Key Vault manage the complexities of key handling, letting organizations focus on their core activities rather than infrastructure.
For organizations that need complete control over their encryption keys, External Key Stores (XKS) allow the use of on-premises key managers to protect cloud resources. This approach, often referred to as "Hold Your Own Keys" (HYOK), ensures that cloud providers cannot access the keys.
Tools like HashiCorp Vault offer centralized workflows for generating and distributing keys across multiple cloud KMS platforms. This minimizes the number of locations where keys are exposed, while improving visibility into the overall infrastructure.
| Feature | Software-Protected (KMS) | Hardware Security Module (HSM) |
|---|---|---|
| Protection Level | FIPS 140-2 Level 1 | FIPS 140-2/3 Level 3 |
| Tenancy | Multi-tenant | Single-tenant (Managed HSM) |
| Control | Cloud provider managed | Customer-managed Security Domain |
| Cost | Lower (~$0.06 per key/month) | Higher (~$1.00–$2.50 per key/month) |
To safeguard keys further, enable soft-delete and purge protection for both HSM and KMS resources. For better performance, applications should retrieve keys once during startup and store them in memory instead of repeatedly querying the HSM.
Eleidon's Key Backup Features
Eleidon offers a secure key backup solution that integrates multi-device synchronization with end-to-end encryption. Designed for industries like law, healthcare, and finance, Eleidon's Vault tackles challenges such as key recovery and compliance while ensuring secure management across devices.
Unlike older email protocols, Eleidon employs mutual whitelisting and cryptographic sender verification using Ed25519 signatures. This creates a phishing-resistant environment. Moreover, its zero-knowledge architecture ensures private keys are generated locally and never leave the user’s device in plaintext. All signing and encryption processes happen client-side.
The Team + Vault plan, priced at $14 per user per month, includes encrypted key backup, multi-device synchronization, and an account recovery guarantee. This automated backup system addresses common issues seen with managed HSMs, where users are often responsible for manual backups and recovery.
For key rotation within the Eleidon ecosystem, users should register a new agent identity and re-verify their associated inbox to maintain a secure chain of trust. Despite the convenience of backup features, it’s recommended to store primary private keys in environment variables or dedicated secrets managers to reduce the risk of accidental exposure.
Compliance and Security Considerations
Meeting Regulatory Standards
Federal agencies and contractors are required to transition all cryptographic modules to FIPS 140-3–compliant systems by September 22, 2026. After this deadline, FIPS 140-2 certifications will no longer be valid for new deployments. This affects any organization handling sensitive data, including healthcare providers under HIPAA and payment processors governed by PCI DSS v4.0.
NIST SP 800-130 outlines the documentation requirements for Cryptographic Key Management Systems (CKMS), focusing on secure key recovery and backup mechanisms. Organizations subject to FISMA must implement comprehensive security programs with strict key management protocols. Similarly, FedRAMP requires FIPS 140–validated cryptography for both data at rest and in transit.
"Data that has been encrypted with lost cryptographic keys will never be recovered. Therefore, it is essential that the application incorporate a secure key backup capability." – CMS Key Management Handbook
Non-compliance with PCI DSS key management requirements (3.6 and 3.7) can result in fines of up to $100,000 per month per incident. Healthcare organizations benefit from the HITECH Act's "safe harbor" provision: encrypted data that meets NIST standards may avoid mandatory breach notifications if compromised.
| Framework | Key Requirement for Backups/Storage | Cryptographic Standard |
|---|---|---|
| FedRAMP | Mandatory FIPS 140-3 validation | NIST SP 800-53 (SC-28) |
| PCI DSS v4.0 | Documented key change and rotation | Requirements 3.6 & 3.7 |
| HIPAA | Addressable encryption implementation | NIST SP 800-111 / 800-57 |
| NIST SP 800-171 | FIPS-validated cryptography for CUI | NIST SP 800-57 |
| FISMA | Regular security control assessments | NIST SP 800-53 |
Organizations handling Controlled Unclassified Information (CUI) must adhere to NIST SP 800-171, which mandates FIPS-validated cryptography for non-federal systems. These requirements emphasize the importance of strong technical safeguards, which are further examined through the CIA triad.
Maintaining the CIA Triad in Backups
To ensure confidentiality, encryption keys must never exist in plaintext during storage. Backup systems achieve this through key wrapping, where Data Encryption Keys (DEKs) are encrypted with Key Encryption Keys (KEKs) before storage. A multi-tier hierarchy - Root Keys securing KEKs, which in turn protect DEKs - reduces the risk of exposing the root of trust.
Integrity measures prevent stored keys from being altered. This is achieved using authenticated encryption modes like AES-GCM or AES-KWP, paired with HMACs to detect tampering. Canonicalization ensures consistency in message formatting before hashing, avoiding discrepancies across platforms.
Availability ensures that keys remain accessible even in cases of loss. This is supported by key escrow, secure duplication within HSM/KMS clusters, and off-site encrypted backups. NIST SP 800-53 highlights the importance of maintaining information availability, often through key escrow practices for recovery.
"Symmetric encryption is only as secure as the keys that power it. Proper key management – generation, storage, use, and retirement of cryptographic keys – is essential to the effective use of cryptography." – Ubiq Security
Separation of duties is critical for compliance, dividing responsibilities among those who manage keys, run backups, and authorize restores. Sensitive operations, like key extraction or root key usage, should employ M-of-N authorization, requiring multiple administrators to approve actions. Restoration processes should include ticket IDs and PAM approval.
Organizations should maintain an inventory of all backup sources, targets, and encryption states to identify risks like unencrypted targets or shared credentials. Periodic "restore with rotated key" drills ensure that data encrypted with older keys remains accessible after key rotations.
Eleidon's Compliance and Security Features
Eleidon's platform incorporates multi-layered backup strategies to enhance compliance and security. Its client-side key management system enforces a zero-knowledge model, ensuring private keys are generated locally and never transmitted to the Eleidon API. Encryption and signing occur entirely on the client side, aligning with GDPR's data minimization principles.
The platform employs Ed25519 digital signatures to establish a cryptographic chain of trust. Each signature generates a 128-character hex value, serving as verifiable proof of identity and integrity. Recipients can confirm authenticity through the X-Eleidon-Signature custom header (v1:agent_id:sig_id:sig_hex), eliminating the need for an API key.
The Team + Vault plan, priced at $14 per user per month, includes encrypted key backup, multi-device synchronization, and an account recovery guarantee. This makes it a strong choice for industries like law, healthcare, and financial services that require secure, compliance-ready messaging.
Eleidon's Trust Request system strengthens security by requiring mutual whitelisting before message delivery. This approach directly counters phishing, which remains the leading cause of data breaches. Additionally, integrations with VirusTotal allow the platform to scan links and attachments for malicious content, adding another layer of protection.
For key rotation, Eleidon users can register a new agent identity and re-verify their inbox to maintain the cryptographic chain of trust. The system assigns a "confidence" score, with a 1.0 rating indicating a valid signature from a verified agent.
Conclusion
Keeping encryption keys secure is at the heart of protecting data. Without proper backups, even a minor mishap could make encrypted information permanently inaccessible. As Axelspire aptly puts it:
"Strong cryptography built on weak key management is security theater. Strong key management supporting strong cryptography delivers actual security."
For organizations managing sensitive data under regulations like HIPAA, PCI DSS v4.0, or FedRAMP, implementing automated lifecycle management, using hardware-backed security such as HSMs, and following solid backup strategies - like the 3-2-1-1-0 rule - is non-negotiable. Ignoring these measures could lead to steep financial penalties. This guide has broken down each phase of the key lifecycle to help ensure these standards are met.
Modern challenges call for advanced solutions, including automated key backups and rotations. Preparing for post-quantum cryptography means having systems that can quickly adapt to new algorithms. With certificate lifespans expected to shrink to just 47 days by 2029, automated rotations will become a necessity. Regular recovery drills are also critical to avoid failures during emergencies.
Effective key backup relies on several key principles: ensuring confidentiality through techniques like key wrapping, maintaining integrity with authenticated encryption methods such as AES-GCM, and guaranteeing availability with geographically distributed backups that use M-of-N authorization.
Platforms like Eleidon showcase how zero-knowledge architecture, client-side key management, and cryptographic verification can safeguard sensitive data. By adopting these practices, organizations can keep encryption keys secure and ensure data is recoverable when it matters most.
FAQs
What’s the fastest way to recover if a key is deleted or lost?
The fastest way to retrieve a deleted or lost encryption key is by restoring it from a backup you’ve created earlier. Keeping regular backups allows you to get back to encrypted operations quickly, especially during disaster recovery. It’s also critical to maintain offline copies of your keys to ensure smooth restoration and reduce downtime in these situations.
How do I choose between HSM-backed keys and software-protected KMS keys?
When deciding between the two, it all comes down to your organization's security, compliance, and operational priorities.
HSM-backed keys provide enhanced security through tamper-resistant hardware, making them a strong choice for protecting sensitive data or meeting stringent compliance standards. On the other hand, software-protected KMS keys are simpler to manage and more budget-friendly, making them a practical option for general encryption needs where the highest level of security isn't a necessity.
To make the right choice, think about factors like key rotation, scalability, and any regulatory requirements your organization must meet. These considerations will help you identify the option that aligns best with your needs.
What key rotation schedule should I follow for DEKs, KEKs, and master keys?
A well-planned key rotation schedule ensures both security and practicality. Data Encryption Keys (DEKs) are best rotated every 90 to 180 days to stay ahead of potential vulnerabilities. Key Encryption Keys (KEKs), on the other hand, are usually rotated once or twice a year. For master keys, given their importance, rotation is less frequent - typically every 1 to 3 years.
To streamline the process, automation is your ally. Use secure methods for key generation and adopt strategies like key versioning and dual key usage to ensure transitions are seamless and compliance is maintained.